如何实现PPPOE虚拟拨号后VPN连接.docx
《如何实现PPPOE虚拟拨号后VPN连接.docx》由会员分享,可在线阅读,更多相关《如何实现PPPOE虚拟拨号后VPN连接.docx(17页珍藏版)》请在冰豆网上搜索。
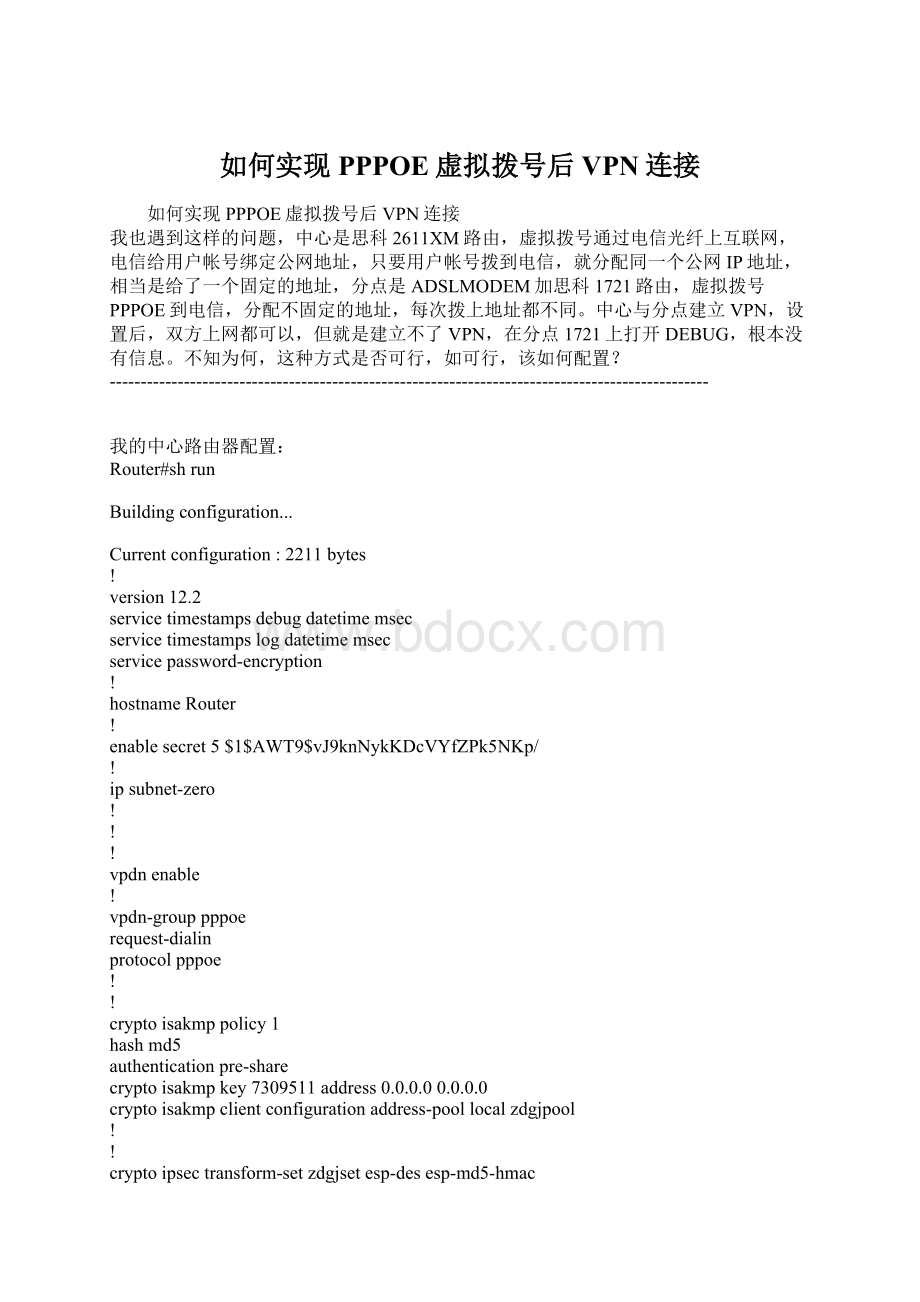
如何实现PPPOE虚拟拨号后VPN连接
如何实现PPPOE虚拟拨号后VPN连接
我也遇到这样的问题,中心是思科2611XM路由,虚拟拨号通过电信光纤上互联网,电信给用户帐号绑定公网地址,只要用户帐号拨到电信,就分配同一个公网IP地址,相当是给了一个固定的地址,分点是ADSLMODEM加思科1721路由,虚拟拨号PPPOE到电信,分配不固定的地址,每次拨上地址都不同。
中心与分点建立VPN,设置后,双方上网都可以,但就是建立不了VPN,在分点1721上打开DEBUG,根本没有信息。
不知为何,这种方式是否可行,如可行,该如何配置?
-------------------------------------------------------------------------------------------------
我的中心路由器配置:
Router#shrun
Buildingconfiguration...
Currentconfiguration:
2211bytes
!
version12.2
servicetimestampsdebugdatetimemsec
servicetimestampslogdatetimemsec
servicepassword-encryption
!
hostnameRouter
!
enablesecret5$1$AWT9$vJ9knNykKDcVYfZPk5NKp/
!
ipsubnet-zero
!
!
!
vpdnenable
!
vpdn-grouppppoe
request-dialin
protocolpppoe
!
!
cryptoisakmppolicy1
hashmd5
authenticationpre-share
cryptoisakmpkey7309511address0.0.0.00.0.0.0
cryptoisakmpclientconfigurationaddress-poollocalzdgjpool
!
!
cryptoipsectransform-setzdgjsetesp-desesp-md5-hmac
!
cryptodynamic-mapzdgjmap10
settransform-setzdgjset
matchaddress115
!
!
cryptomapzdgjtransclientconfigurationaddressinitiate
cryptomapzdgjtransclientconfigurationaddressrespond
cryptomapzdgjtrans1ipsec-isakmpdynamiczdgjmap
!
!
!
!
!
!
!
mtareceivemaximum-recipients0
!
!
!
!
interfaceFastEthernet0/0
ipaddress10.10.1.139255.255.255.0
ipnatinside
duplexauto
speedauto
!
interfaceFastEthernet0/1
noipaddress
duplexauto
speedauto
pppoeenable
pppoe-clientdial-pool-number1
!
interfaceDialer1
ipaddressnegotiated
ipnatoutside
encapsulationppp
dialerpool1
dialer-group1
nocdpenable
pppauthenticationpapcallin
ppppapsent-usernamezdgjpassword7055C545F721C1E59
cryptomapzdgjtrans
!
iplocalpoolzdgjpool192.168.10.1192.168.10.254
ipnatinsidesourceroute-mapnonatinterfaceDialer1overload
ipclassless
iproute0.0.0.00.0.0.0Dialer1
iphttpserver
!
!
access-list115permitip10.10.0.00.0.255.255192.168.100.00.0.0.255
access-list115permitip10.10.0.00.0.255.255192.168.200.00.0.0.255
access-list115permitip192.168.10.00.0.0.255192.168.200.00.0.0.255
access-list115permitip192.168.10.00.0.0.255192.168.100.00.0.0.255
access-list120denyip10.10.0.00.0.255.255192.168.100.00.0.0.255
access-list120denyip10.10.0.00.0.255.255192.168.200.00.0.0.255
access-list120permitip10.10.0.00.0.255.255any
dialer-list1protocolippermit
!
route-mapnonatpermit10
matchipaddress120
!
callrsvp-sync
!
!
mgcpprofiledefault
!
!
!
dial-peercorcustom
!
!
!
!
!
linecon0
lineaux0
linevty04
password7031E5F0C0C5E731F
login
!
!
end
Router#
Router#
--------------------------------------------------------------------------------------
我的分点路由器配置:
Buildingconfiguration...
Currentconfiguration:
1464bytes
!
version12.2
servicetimestampsdebugdatetimemsec
servicetimestampslogdatetimemsec
servicepassword-encryption
!
hostnameRouter
!
loggingqueue-limit100
!
ipsubnet-zero
!
!
!
vpdnenable
!
vpdn-grouppppoe
request-dialin
protocolpppoe
!
!
!
!
!
cryptoisakmppolicy1
hashmd5
authenticationpre-share
cryptoisakmpkey7309511addressx.x.x.x
!
!
cryptoipsectransform-setzdgjsetesp-desesp-md5-hmac
!
cryptomapzdgjtrans1ipsec-isakmp
setpeerx.x.x.x
settransform-setzdgjset
matchaddress115
!
!
!
!
interfaceEthernet0
noipaddress
half-duplex
pppoeenable
pppoe-clientdial-pool-number1
!
interfaceFastEthernet0
ipaddress192.168.100.1255.255.255.0
ipnatinside
speedauto
!
interfaceDialer1
ipaddressnegotiated
ipmtu1492
ipnatoutside
encapsulationppp
dialerpool1
dialer-group1
ppppapsent-usernamewangcdpassword700554A51560B53545B
cryptomapzdgjtrans
!
ipnatinsidesourceroute-mapnonatinterfaceDialer1overload
ipclassless
iproute0.0.0.00.0.0.0Dialer1
noiphttpserver
noiphttpsecure-server
!
!
!
access-list115permitip192.168.100.00.0.0.25510.10.1.00.0.0.255
access-list115denyip192.168.100.00.0.0.255any
access-list120denyip192.168.100.00.0.0.25510.10.1.00.0.0.255
access-list120permitip192.168.100.00.0.0.255any
!
route-mapnonatpermit10
matchipaddress120
!
!
linecon0
lineaux0
linevty04
!
noschedulerallocate
end
Router#
上网没问题,打开DEBUG没有任何信息
debugcryptoipsec
debugcryptoisakmp
debugcryptoengine
-----------------------------------------------------------------------------------
在hubtospoke的结构中,要实现spoketospoke通讯当然要求所有spoke也要有静态的IP的说,这里已经有一位兄弟作个这个测试了,ZT出来给大家看看的说:
关于四台Cisco防火墙实现VPN网络的实施
其实四台Cisco防火墙的VPN同两台防火墙做VPN没什么大的区别,只是一定要注意路由的配置(我就是在这上面花了很长的时间,不是多写就是少写了,多少都是不会通的);在四台Ciscopix做VPN中,有两种方式,一种是采用一个中心的方式,另一种就是分散式的(我自己起的名字J),前者,也就是说以一个PIX点为中心,其它的机器都连到本机上,在通过本机做路由;后者,则是在每一个路由上都要写出到另外三台的加密方式(听来就很麻烦),这里我采用的就是第一种类型(不是我偷懒,而是客户要求,谁让客户是上帝了呢!
);
以下,是施工图以及四个Ciscopix的详细配置:
详细配置如下:
中心pix1:
:
Saved
:
Writtenbyenable_15at23:
10:
31.763UTCThuApr242003
PIXVersion6.2
(2)
nameifethernet0outsidesecurity0
nameifethernet1insidesecurity100
enablepasswordNHvIO9dsDwOK8b/kencrypted
passwdNHvIO9dsDwOK8b/kencrypted
hostnamepixfirewall
fixupprotocolftp21
fixupprotocolhttp80
fixupprotocolh323h2251720
fixupprotocolh323ras1718-1719
fixupprotocolils389
fixupprotocolrsh514
fixupprotocolrtsp554
fixupprotocolsmtp25
fixupprotocolsqlnet1521
fixupprotocolsip5060
fixupprotocolskinny2000
names
access-list101permitip172.17.0.0255.255.0.0172.16.0.0255.255.0.0
access-list101permitip172.17.5.0255.255.255.0172.17.10.0255.255.255.0
access-list101permitip172.17.10.0255.255.255.0172.17.5.0255.255.255.0
access-list101permitip172.16.0.0255.255.0.0172.17.0.0255.255.0.0
access-list101permitip172.17.5.0255.255.255.0172.17.17.0255.255.255.0
access-list101permitip172.17.10.0255.255.255.0172.17.17.0255.255.255.0
access-listhyzcpermiticmpanyany
access-listhyzcpermittcpanyany
access-listhyzcpermitudpanyany
pagerlines24
interfaceethernet0auto
interfaceethernet1auto
mtuoutside1500
mtuinside1500
ipaddressoutside192.168.0.2255.255.255.240
ipaddressinside172.17.5.1255.255.255.0
ipauditinfoactionalarm
ipauditattackactionalarm
pdmhistoryenable
arptimeout14400
nat(outside)10.0.0.00.0.0.000
nat(inside)10.0.0.00.0.0.000
access-grouphyzcininterfaceoutside
routeoutside0.0.0.00.0.0.0218.7.16.491
routeinside172.17.0.0255.255.0.0172.17.5.201
routeoutside172.17.17.0255.255.255.0192.168.0.41
routeoutside172.17.16.0255.255.255.0192.168.0.11
routeoutside172.16.0.0255.255.255.0192.168.0.31
routeoutside172.17.18.0255.255.255.0218.7.16.521
routeoutside172.17.18.64255.255.255.0218.7.16.491
routeoutside218.7.248.100255.255.255.252218.7.16.491
timeoutxlate3:
00:
00
timeoutconn1:
00:
00half-closed0:
10:
00udp0:
02:
00rpc0:
10:
00h3230:
05:
00sip0:
30:
00sip_media0:
02:
00
timeoutuauth0:
05:
00absolute
aaa-serverTACACS+protocoltacacs+
aaa-serverRADIUSprotocolradius
aaa-serverLOCALprotocollocal
nosnmp-serverlocation
nosnmp-servercontact
snmp-servercommunitypublic
nosnmp-serverenabletraps
floodguardenable
sysoptconnectionpermit-ipsec
nosysoptroutednat
cryptoipsectransform-setstrongesp-desesp-sha-hmac
cryptomaptohyjt20ipsec-isakmp
cryptomaptohyjt20matchaddress101
cryptomaptohyjt20setpeer192.168.0.3
cryptomaptohyjt20setpeer192.168.0.4
cryptomaptohyjt20setpeer192.168.0.1
cryptomaptohyjt20settransform-setstrong
cryptomaptohyjtinterfaceoutside
isakmpenableoutside
isakmpkeyciscoaddress192.168.0.3netmask255.255.255.255
isakmpkeyciscoaddress192.168.0.4netmask255.255.255.255
isakmpkeyciscoaddress192.168.0.1netmask255.255.255.255
isakmpidentityaddress
isakmppolicy9authenticationpre-share
isakmppolicy9encryptiondes
isakmppolicy9hashsha
isakmppolicy9group1
isakmppolicy9lifetime86400
telnet218.7.16.49255.255.255.255inside
telnet172.17.5.20255.255.255.255inside
telnettimeout5
sshtimeout5
terminalwidth80
Cryptochecksum:
8982919a8bfa10ba09cddee3f2da0e6a
:
end
pix2配置:
:
Saved
:
Writtenbyenable_15at00:
00:
48.042UTCFriApr252003
PIXVersion6.2
(2)
nameifethernet0outsidesecurity0
nameifethernet1insidesecurity100
enablepasswordN.swjdczcTdUzgrSencrypted
passwdN.swjdczcTdUzgrSencrypted
hostnameHYZCrc
fixupprotocolftp21
fixupprotocolhttp80
fixupprotocolh323h2251720
fixupprotocolh323ras1718-1719
fixupprotocolils389
fixupprotocolrsh514
fixupprotocolrtsp554
fixupprotocolsmtp25
fixupprotocolsqlnet1521
fixupprotocolsip5060
fixupprotocolskinny2000
names
access-list101permitip172.17.17.0255.255.255.0172.17.10.0255.255.255.0
access-list101permitip172.17.17.0255.255.255.0172.17.5.0255.255.255.0
access-listhyzcpermiticmpanyany
access-listhyzcpermittcpanyany
access-listhyzcpermitudpanyany
pagerlines24
interfaceethernet0auto
interfaceethernet1auto
mtuoutside1500
mtuinside1500
ipaddressoutside192.168.0.4255.255.255.252
ipaddressinside172.17.17.254255.255.255.0
ipauditinfoactionalarm
ipauditattackactionalarm
pdmhistoryenable
arptimeout14400
nat(outside)10.0.0.00.0.0.000
nat(inside)0access-list101
nat(inside)10.0.0.00.0.0.000
routeoutside0.0.0.00.0.0.0218.7.37.51
timeoutxlate3:
00:
00
timeoutconn1:
00:
00half-closed0:
10:
00udp0:
02:
00rpc0:
10:
00h3230:
05:
00sip0:
30:
00sip_media0:
02:
00
timeoutuauth0:
05:
00absolute
aaa-serverTACACS+protocoltacacs