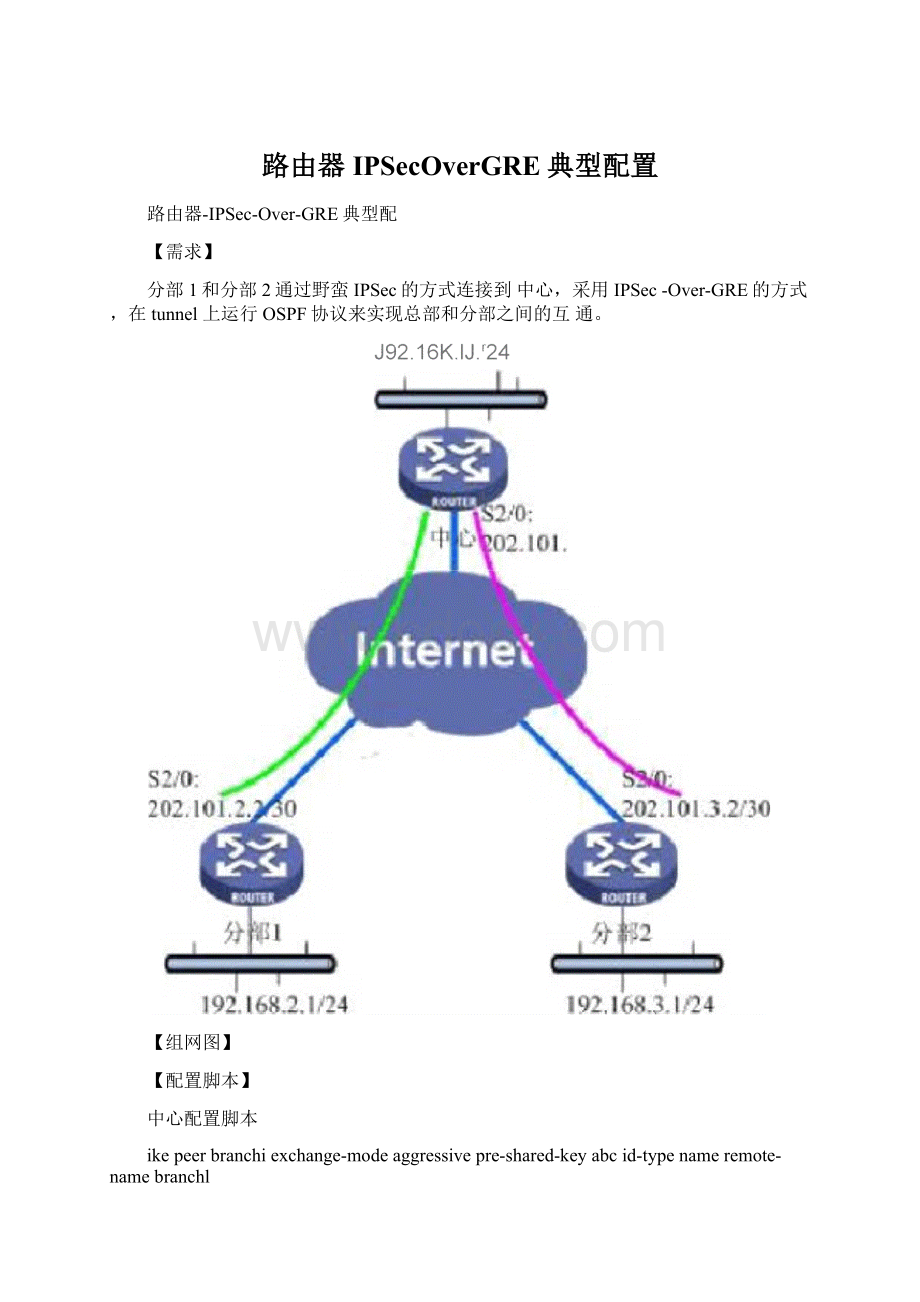
路由器IPSecOverGRE典型配置Word文件下载.docx
《路由器IPSecOverGRE典型配置Word文件下载.docx》由会员分享,可在线阅读,更多相关《路由器IPSecOverGRE典型配置Word文件下载.docx(18页珍藏版)》请在冰豆网上搜索。
link-protocolppp
ipaddress202.101.1.2255.255.255.252
interfaceTunnelO
ipaddress10.0.0.1255・255.255.252source202.101・1・2
destination202・101.2.2
ipsecpolicybranchi
interfaceTunnell
ipaddress10.0・0・5255.255.255.252source202.101・1・2
destination202.101・3・2
ipsecpolicybranch2
/配置中心和分部1之间的GREtunnel/
/在tunnel0上应用IPSecpolicybranchi/
/配置中心和分部2之间的GREtunnel/
/在tunnel1上应用IPSecpolicybranch2/
/中心的内网地址/
/分部1属于area10/
/分部2属于area20/
/总部属于area0/
interfaceNULL0
interfaceLoopBackO
ipaddress1.1.1.1255.255.255.255
interfaceEthernet0/0
ipaddress192.168・1・1255.255.255・0
ospf1
area0.0.0.10
network10.0.0.00.0.0.3
area0.0.0.20
network10.0.0.40.0.0.3
area0.0.0.0
network1.1.1.10.0.0.0
sysnameCenter
ikelocal-namecenter
routerid1.1.1.1
radiusschemesystem
domainsystem
#|
iproute-static0.0.0.00.0.0.0202.101.1.1preference60
user-interfacecon0
user-interfacevty04
return
/中心ike的local-name为:
center/
分部1配置脚本
sysnameBranch1
ikelocal-namebranch1
ikepeercenter
exchange-modeaggressivepre-shared-keyabcid-typenameremote-namecenterremote-address10.0.0.1
ipsecpolicybranch110isakmp
securityacl3001
ike-peercenter
rule0permitipsource192.168.2.0
interfaceSerial2/0link-protocolppp
ipaddress202.101.2.2255.255.255.252
interfaceTunnel0
ipaddress10.0.0.2255.255.255.252
source202.101.2.2destination202.101.1.2
ipsecpolicybranch1
interfaceLoopBack0
ipaddress2.2.2.2255.255.255.255
ipaddress192.168.2.1255.255.255.0
/分部1的ike的local-name为:
branch"
/配置到中心的ikepeer/
/设置IPSec为野蛮方式/
/预共享密钥为
/选择名字作为
/对端的名字为
/对端的地址为
abc/
ike协商过程中使用的ID/
10.0.0.1(中心的tunnel地址)/
/定义ipsecproposal/
/配置到中心的ipsecpolicy/
/指定安全策略所引用的访问控制列表号/
/弓丨用ikepeer/
/弓丨用ipsecproposal/
/定义从分部1到中心的内网数据流/
0.0.0.255destination192.168.1.00.0.0.255
/配置分部1和中心之间的GREtunnel/
/在tunnel0上应用IPSecpolicybranchi/
/配置分部1的内网地址/
area0.0.0.10/分部1属于area10/
network2.2220.0.0.0
network192.168.2.00.0.0.255
iproute-static0.0.0.00.0.0.0202.101.2.1preference60
分部2配置脚本
sysnameBranch2
/分部2的ike的local-name为:
branch2/
exchange-modeaggressive
pre-shared-keyabc
id-typename
remote-namecenter
/对端的名字为center/
remote-address10.0.0.5
/对端的地址为10.0.0.5(中心的tunnel地址)/
/定义从分部2到中心的GRE数据流/
rule0permitipsource192.168.3.0
ipaddress202.101.3.2255.255.255.252
ipaddress10.0.0.6255.255.255.252
source202.101.3.2
destination202.101.1.2
ipaddress3.333255.255.255.255
/在tunnel0上应用IPSecpolicybranch2/
ipaddress192.168.3.1255.255.255.0
network3.3.3.30.0.0.0
network192.168.3.00.0.0.255
iproute-static0.0.0.00.0.0.0202.101.3.1preference60
【验证】
1、中心上的ikesa状态:
dispikesa
connection-idpeer
flagphasedoi
44
10.0.0.2
RD
1
IPSEC
48
10.0.0.6
2
47
45
flagmeaning
RD--READYST--STAYALIVE
RL--REPLACEDFD--FADINGTOTIMEOUT
2、中心上的IPSecsa状态:
dispipsecsa
Interface:
Tunnel0pathMTU:
64000
IPsecpolicyname:
"
branchl"
sequeneenumber:
10
mode:
isakmp
connectionid:
8
encapsulationmode:
tunnelperfectforwardsecrecy:
Nonetunnel:
localaddress:
10.0.0.1
remoteaddress:
10.0.0.2
flow:
(4timesmatched)
souraddr:
192.168.1.0/255.255.255.0port:
0protocol:
IP
destaddr:
192.168.2.0/255.255.255.0port:
[inboundESPSAs]
spi:
2701983530(0xa10cff2a)
proposal:
ESP-ENCRYPT-DES
ESP-AUTH-MD5
saremainingkeyduration
(bytes/sec):
1887436664/2136
maxreceivedsequenee-number:
udpencapsulationusedfornat
traversal:
N
[outboundESPSAs]
2132567950(0x7f1c678e)
1887436632/2136
maxsentsequenee-number:
3
TunnellpathMTU:
branch2"
9
10.0.0.5
10.0.0.6
(18times
matched)
192.168.3.0/255.255.255.0port:
1612204948(0x60184b94)
1887436188/2886
9
3432409622(0xcc966a16)proposal:
1887436044/2886
N3、中心路由表
dispiprout
RoutingTable:
publicnet
Destination/MaskProtocol
PreCostNexthopInterfa
ce
0.000/0STATIC600
202.101.1.1Serial2/0/0
1.1.1.1/32DIRECT00
127.0.0.1InLoopBack0
2.222/32OSPF101563
10.0.0.2Tunnel0
3.3.3.3/32OSPF101563
Tunnel1
10.0.0.0/30
DIRECT00
10.0.0.1
Tunnel0
10.0.0.1/32
127.0.0.1
InLoopBack0
10.0.0.4/30
10.0.0.5
10.0.0.5/32
127.0.0.0/8
127.0.0.1/32
DIRECT
192.168.1.0/24
DIRECT0
192.168.1.1
LoopBack10
192.168.1.1/32
192.168.2.0/24
OSPF10
1563
192.16830/24OSPF10156310.0.0.6Tunnel1
202.101.1.0/30DIRECT00
202.101.1.2Serial2/0/0
202.101.1.1/32DIRECT00
202.101.1.2/32DIRECT00
状态:
peer
4、分部1的ikesadispikesa
connection-idflagphasedoi
5、分部1的ipsecsa状态:
6
192.16820/255.255.255.0port:
1887436664/2054
1887436632/2054
N6、分部1的路由表:
publicnetDestination/MaskProtocolPreCostNexthopInter
face
0.0.0.0/0
202.101.2.1
1.1.1.1/32
2.2.2.2/32
3.3.3.3/32
10.0.0.2/32
10.0.0.4/30OSPF103124
10.0.0.1Tunnel0
127.0.0.0/8DIRECT00
127.0.0.1/32DIRECT00
192.168.1.0/24OSPF10156310.0.0.1Tunnel0
192.168.2.0/24DIRECT00
192.168.2.1LoopBack10
192.168.2.1/32DIRECT00
192.168.3.0/24OSPF10312510.0.0.1Tunnel0
202.101.2.0/30DIRECT00
202.101.2.2Serial2/0/0
202.101.2.1/32DIRECT00
202.101.2.1Serial2/0/0
202.101.2.2/32DIRECT00
【提示】
1、IPSec-Over-GRE和GRE-Over-IPSec方式配置上的区别为:
GRE-Over-IPS
ec
IPSec-Over-G
RE
ACL定义
GRE数据流
内网数据流
Ikepeer中指
对方公网地址
对方GRE
定的
remote-addre
tunnel地址
ss
应用端口
公网出口
GREtunnel上
2、各个分部和总部之间通过OSPF路由来实现
互访,如果没有运行OSPF则必需在分部和总部配置静态路由。
【Center配置】
iproute-stati