实验8广域网VPNIPSec网络综合实验.docx
《实验8广域网VPNIPSec网络综合实验.docx》由会员分享,可在线阅读,更多相关《实验8广域网VPNIPSec网络综合实验.docx(17页珍藏版)》请在冰豆网上搜索。
实验8广域网VPNIPSec网络综合实验
实验八广域网VPN(IPSec)网络综合实验
【实验名称】
广域网VPN(IPSec)网络综合实验
【实验原型】
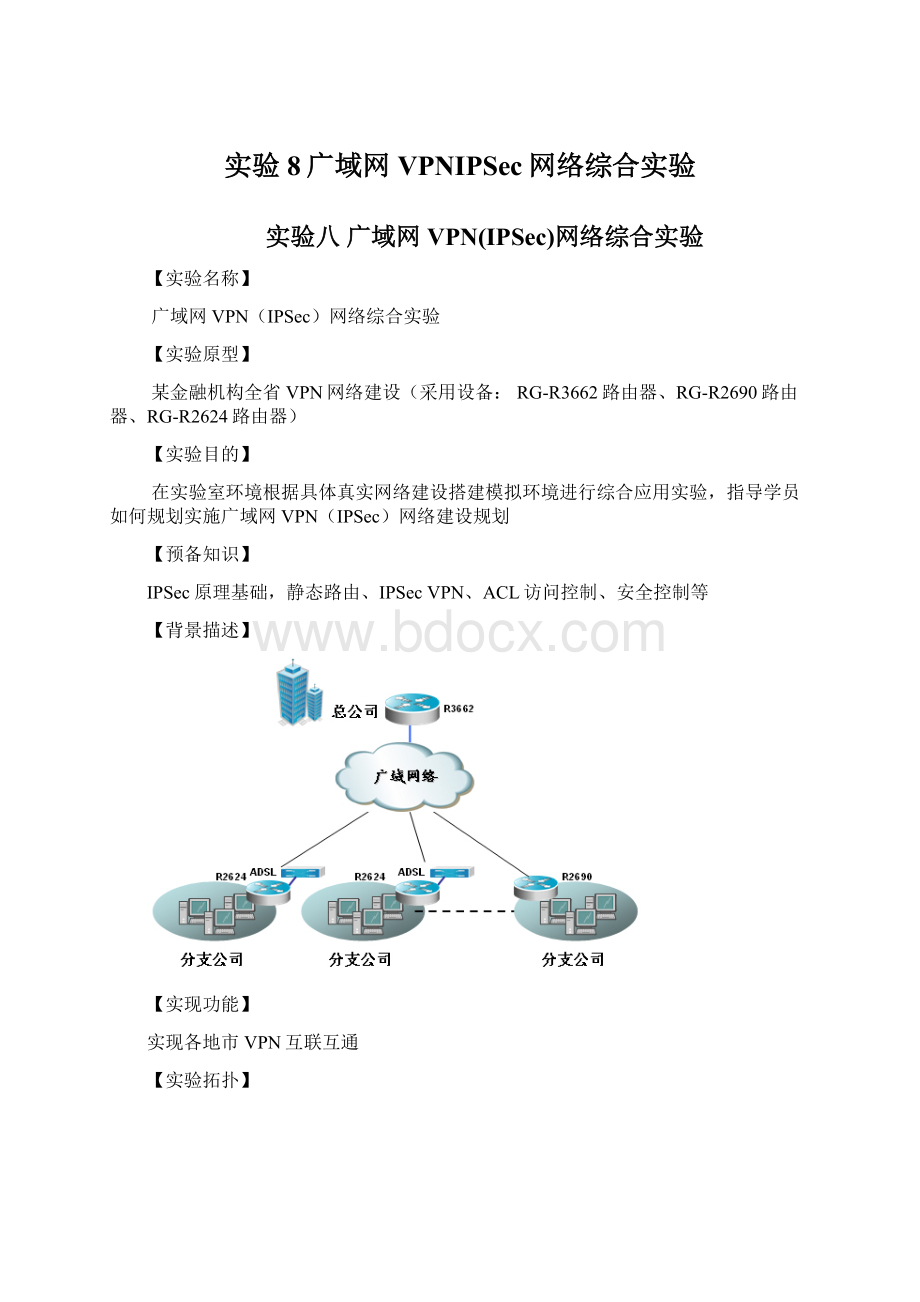
某金融机构全省VPN网络建设(采用设备:
RG-R3662路由器、RG-R2690路由器、RG-R2624路由器)
【实验目的】
在实验室环境根据具体真实网络建设搭建模拟环境进行综合应用实验,指导学员如何规划实施广域网VPN(IPSec)网络建设规划
【预备知识】
IPSec原理基础,静态路由、IPSecVPN、ACL访问控制、安全控制等
【背景描述】
【实现功能】
实现各地市VPN互联互通
【实验拓扑】
【实验设备】
核心设备:
R36621台;接入设备:
R26242台;S3550-241台;实验PC:
3台;
该实验采用三台路由器分别命名为R3642-A,R2624-B,R2624-C;其中R3642-A做VPNServer,R2624-B,R2624-C做VPNClient;交叉双绞线2条,直连双绞线8条;在每台路由器内部分别部署一台测试PC,IP地址为192.168.X..200/24(其中192.168.X..0为路由器内部网络);IP地址如下规划:
设备
相关描述
IP地址
备注
R3642-A
E0
10.0.0.10/30
\
E1
10.0.0.6/30
\
E3
192.168.2.254/24
\
R2624-B
E0
192.168.0.254/24
\
E1
10.0.0.5/30
\
R2624-C
E0
192.168.1.254/24
\
E1
10.0.0.9/30
\
测试PC1
\
192.168.0.200/24
接在R3642-A上的测试PC
测试PC2
\
192.168.2.200/24
接在R2624-B上的测试PC
测试PC2
2624-C接口E0
192.168.1.200/24
接在R2624-B上的测试PC
【实验步骤】
IPSec的配置包括在每一台路由器上执行以下步骤:
第一步路由器基本配置
第二步IKEPhaseIPolicy与IKEPhaseIIPolicy配置
第三步网络接口启用VPN功能
第四步测试VPN功能
第一步路由器的基本配置
(1)R3642-A路由器基本配置
conft
hostnameR3642-A
!
enablepasswordstar
!
interfaceFastEthernet0
ipaddress10.0.0.10255.255.255.252
noshut
exit
interfaceFastEthernet1
ipaddress10.0.0.6255.255.255.252
noshut
exit
interfaceFastEthernet3
ipaddress192.168.2.254255.255.255.0
noshut
exit
!
iproute192.168.0.0255.255.255.010.0.0.5
iproute192.168.1.0255.255.255.010.0.0.9
!
linevty04
passwordstar
login
end
(2)R2624-B路由器基本配置
conft
hostnameR2624-B
!
enablepasswordstar
!
interfaceFastEthernet0
ipaddress192.168.0.254255.255.255.252
noshut
exit
!
interfaceFastEthernet1
ipaddress10.0.0.5255.255.255.252
noshut
exit
!
iproute0.0.0.00.0.0.010.0.0.6
!
linevty04
passwordstar
login
end
(3)R2624-C路由器的基本配置
conft
hostnameR2624-C
!
interfaceFastEthernet0
ipaddress192.168.1.254255.255.255.0
noshut
exit
!
interfaceFastEthernet1
ipaddress10.0.0.9255.255.255.0
exit
!
iproute0.0.0.00.0.0.010.0.0.10
!
linevty04
passwordstar
login
end
第二步路由器IKEPhaseIPolicy与IKEPhaseIIPolicy配置
(1)配置R3642-AIKEPhaseIPolicy
cryptoisakmppolicy10
!
设定路由图策略,确保两端的IKE配置一致
authenticationpre-share
!
设置为共享认证模式
hashmd5
!
Hash散列算法设定为MD5
group2
!
设定Diffie-Hellman密钥交换
exit
cryptoisakmpkeystaraddress10.0.0.5
!
指定对端VPN设备的预共享密钥和IP地址,确保两边的预共享key一致
cryptoisakmpkeystaraddress10.0.0.9
(2)配置R3642-AIKEPhaseIIPolicy
cryptoipsectransform-setstar-netesp-desesp-md5-hmac
!
启用ESP加密安全载荷IPSec转换规则
access-list101permitip192.168.2.00.0.0.255192.168.0.00.0.0.255
!
通过路由器的VPN感兴趣流控制列表
access-list102permitip192.168.2.00.0.0.255192.168.1.00.0.0.255
!
通过路由器的VPN感兴趣流控制列表
cryptomapstar-net10ipsec-isakmp
!
指定加密图名称启用IPSec
setpeer10.0.0.5
!
建立VPN对等体
settransform-setstar-net
!
设定加密图匹配IPSes转换规则
matchaddress101
!
设定加密图匹配VPN感兴趣流列表
exit
!
cryptomapstar-net20ipsec-isakmp
!
定义加密图策略20
setpeer10.0.0.9
!
建立VPN对等体
settransform-setstar-net
!
设定加密图匹配IPSec转换规则
matchaddress102
!
设定加密图匹配VPN感兴趣流列表
exit
(3)配置R2624-BIKEPhaseIPolicy
cryptoisakmppolicy10
hashmd5
group2
exit
cryptoisakmpkeystaraddress10.0.0.6
(4)配置R2624-BIKEPhaseIIPolicy
cryptoipsectransform-setstaresp-desesp-md5-hmac
cryptomapstar10ipsec-isakmp
setpeer10.0.0.6
settransform-setstar
matchaddress101
exit
access-list101permitip10.1.2.00.0.0.25510.1.1.00.0.0.255
!
(5)配置R2624-CIKEPhaseIPolicy
cryptoisakmppolicy10
authenticationpre-share
hashmd5
group2
exit
!
cryptoisakmpkeystaraddress10.0.0.10
(6)配置R2624-CIKEPhaseIIPolicy
cryptoipsectransform-setstar-netesp-desesp-md5-hmac
cryptomapstar-net10ipsec-isakmp
setpeer10.0.0.1
settransform-setstar-net
matchaddress101
exit
!
access-list101permitip192.168.1.00.0.0.255192.168.2.00.0.0.255
!
第三、网络接口启用VPN
(1)配置R3642-A网络接口Fa0,Fa1启用VPN
interfaceFastEthernet0
ipaddress10.0.0.10255.255.255.252
noshut
cryptomapstar-net
exit
!
interfaceFastEthernet1
ipaddress10.0.0.6255.255.255.252
noshut
cryptomapstar-net
exit
!
(2)配置R2624-B网络接口Fa1启用VPN
interfaceFastEthernet1
ipaddress10.0.0.5255.255.255.252
noshut
cryptmapstar
exit
!
(3)网络接口Fa1启用VPN功能
interfaceFastEthernet1
ipaddress10.0.0.9255.255.255.0
cryptomapstar-net
noshut
exit
!
第四测试VPN功能
(1)通过测试PC之间通信,测试VPN功能。
此次测试我们从R2624-B内部主机192.168.0.200/24使用ping命令批pingR3642-A内部主机192.168.2.200,ping使用参数“–t”。
(2)在路由器上打开Debugcryptoisakmp和DebugcryptoIpsec两条Debug命令,可以看到相关调试信息。
注:
VPN连接成功的调试信息需要用到以下俩条命令:
clearcryptoisa和clearcryptosa;通过这两条命令才可以看到完整的调试信息;
VPN连接成功的Debug信息
R2624-B#
Getacquire:
192.168.0.0/0.0.0.255->192.168.2.0/0.0.0.255,prot0,port0/0
——发出第一个协商消息mainI1
Acqurirenegociatewith10.0.0.6
(33)beginningMainModeexchange
(33)sendingpacketto10.0.0.6(I)MM_SI1_WR1,MM_SA_SETUP
sendoutmainI1,andwaitR1
(33)receivedpacketfrom10.0.0.6->10.0.0.5,(I)MM_SI1_WR1,MM_SA_SETUP
——处理对方响应消息MR1
Exchangetype:
0x2
payloadformat:
,
mainr1process
(33)CheckingISAKMPtransform1againstpriority10policy
——检查响应方回来的IKE协商策略
encryptionDES-CBC
hashMD5
authpre-share
group2
lifetypeinseconds
lifeduration86400orginal:
86400
——表示IKE协商策略接受
(33)attsareacceptable
——检查IKE协商策略通过,发送MI2
(33)sendingpacketto10.0.0.6(I)MM_SI2_WR2,MM_KEY_EXCH
(33)receivedpacketfrom10.0.0.6->10.0.0.5,(I)MM_SI2_WR2,MM_KEY_EXCH
——收到了响应方的MR2
Exchangetype:
0x2
payloadformat:
,
respondhandlemaini2
(33)processingNONCEpayload.
(33)processingKEpayload.messageID=0
(33)SKEYIDstategenerated
(33)sendingpacketto10.0.0.6(I)MM_SI3_WR3,MM_VERIFY
(33)receivedpacketfrom10.0.0.6->10.0.0.5,(I)MM_SI3_WR3,MM_VERIFY
——验证MR2通过发送MI3
——收到响应方的MR3
Exchangetype:
0x2
payloadformat:
,
(33)sendingpacketto10.0.0.6(I)QM_IDLE
(33)Phase_1negotiatecomplete!
——检查MR3通过,完成阶段一的协商
——发出阶段二协商的第一消息QI1
(33)BeginningQuickModeexchange,M-IDof66
(33)sendingpacketto10.0.0.6(I)QM_SI1_WR1
——收到对方的响应消息QR1
(33)receivedpacketfrom10.0.0.6->10.0.0.5,(I)QM_SI1_WR1
Exchangetype:
0x20
——验证QR1,通过,发起方完成阶段二的协商
payloadformat:
,
Receivenotify:
ipsecresponderlifetime.(
33)processingSApayload.messageID=66
(33)CreatingIPSecSAs.
inboundSAhasspi8866
protocolesp,DES_CBC
authMD5
outboundSAhasspi923
protocolesp,DES_CBC
authMD5
lifetimeof3600seconds,soft3570seconds
lifetimeof4608000kilobytes,soft256kilobytes
——完成阶段二的协商,并发送最后一个协商消息QI2
(33)sendingpacketto10.0.0.6(I)QM_IDLE
(33)Phase_2negotiatecomplete!
【问题与思考】
理解VPN的原理,掌握IPsec的原理;
【参考配置】
R3642-A#
R3642-A#showrun
Buildingconfiguration...
Currentconfiguration:
!
version6.14
(2)
!
hostname"R3642-A"
!
enablepasswordstar
!
!
!
ipsubnet-zero
!
!
cryptoisakmppolicy10
hashmd5
group2
cryptoisakmpkeystaraddress10.0.0.9
cryptoisakmpkeystaraddress10.0.0.5
cryptoipsectransform-setstar-netesp-desesp-md5-hmac
cryptomapstar-net10ipsec-isakmp
setpeer10.0.0.5
settransform-setstar-net
matchaddress101
!
cryptomapstar-net20ipsec-isakmp
setpeer10.0.0.9
settransform-setstar-net
matchaddress102
!
!
interfaceFastEthernet0
ipaddress10.0.0.10255.255.255.252
cryptomapstar-net
!
interfaceFastEthernet1
ipaddress10.0.0.6255.255.255.252
cryptomapstar-net
!
interfaceFastEthernet2
noipaddress
shutdown
!
interfaceFastEthernet3
ipaddress192.168.2.254255.255.255.0
!
interfaceSerial0
noipaddress
shutdown
!
interfaceSerial1
noipaddress
shutdown
!
ipclassless
iproute192.168.0.0255.255.255.010.0.0.5
iproute192.168.1.0255.255.255.010.0.0.9
access-list101permitip192.168.2.00.0.0.255192.168.0.00.0.0.255
access-list102permitip192.168.2.00.0.0.255192.168.1.00.0.0.255
!
linecon0
lineaux0
linevty04
passwordstar
login
!
End
R2624-B#showrun
Buildingconfiguration...
Currentconfiguration:
!
version6.14
(2)
!
hostname"R2624-B"
!
enablepasswordstar
!
!
!
ipsubnet-zero
!
!
cryptoisakmppolicy10
hashmd5
group2
cryptoisakmpkeystaraddress10.0.0.6
cryptoipsectransform-setstaresp-desesp-md5-hmac
cryptomapstar10ipsec-isakmp
setpeer10.0.0.6
settransform-setstar
matchaddress101
!
!
interfaceFastEthernet0
ipaddress192.168.0.254255.255.255.0
!
interfaceFastEthernet1
ipaddress10.0.0.5255.255.255.252
cryptomapstar
!
interfaceFastEthernet2
noipaddress
shutdown
!
interfaceFastEthernet3
noipaddress
shutdown
!
interfaceSerial0
noipaddress
shutdown
!
interfaceSerial1
noipaddress
shutdown
!
ipclassless
iproute0.0.0.00.0.0.010.0.0.6
access-list101permitip192.168.0.00.0.0.255192.168.2.00.0.0.255
!
linecon0
lineaux0
linevty04
passwordstar
login
!
end
R2624-C#
R2624-C#showrun
Buildingconfiguration...
Currentconfiguration:
!
!
hostname"R2624-C"
!
enablepasswordstar
!
!
!
ipsubnet-zero
!
!
cryptoisakmppolicy10
hashmd5
group2
cryptoisakmpkeystaraddress10.0.0.10
cryptoipsectransform-setstar-netesp-desesp-md5-hmac
cryptomapstar-net10ipsec-isakmp
setpeer10.0.0.1
settransform-setstar-net
matchaddress101
!
!
interfaceFastEthernet0
ipaddress192.168.1.254255.255.255.0
!
interfaceFastEthernet1
ipaddress10.0.0.9255.255.255.0
cryptomapstar-net
!
interfaceFastEthernet2
noipaddress
shutdown
!
interfaceFastEthernet3
noipaddress
shutdown
!
interfaceSerial0
noipaddress
shutdown
!
interfaceSerial1
noipaddress
shutdown
!
ipclassless
iproute0.0.0.00.0.0.010.0.0.10
access-list101permiti