数字证书 学习笔记.docx
《数字证书 学习笔记.docx》由会员分享,可在线阅读,更多相关《数字证书 学习笔记.docx(11页珍藏版)》请在冰豆网上搜索。
数字证书学习笔记
数字证书学习笔记
1.工具准备
1.1软件下载
JDK
OPenSSL
1.2环境变量配置
JAVA_HOME:
C:
\ProgramFiles\Java\jdk1.7.0_07
OpenSSL_HOME:
D:
\ProgramFiles\openssl
Path:
%JAVA_HOME%\bin;%OpenSSL_HOME%\bin;......
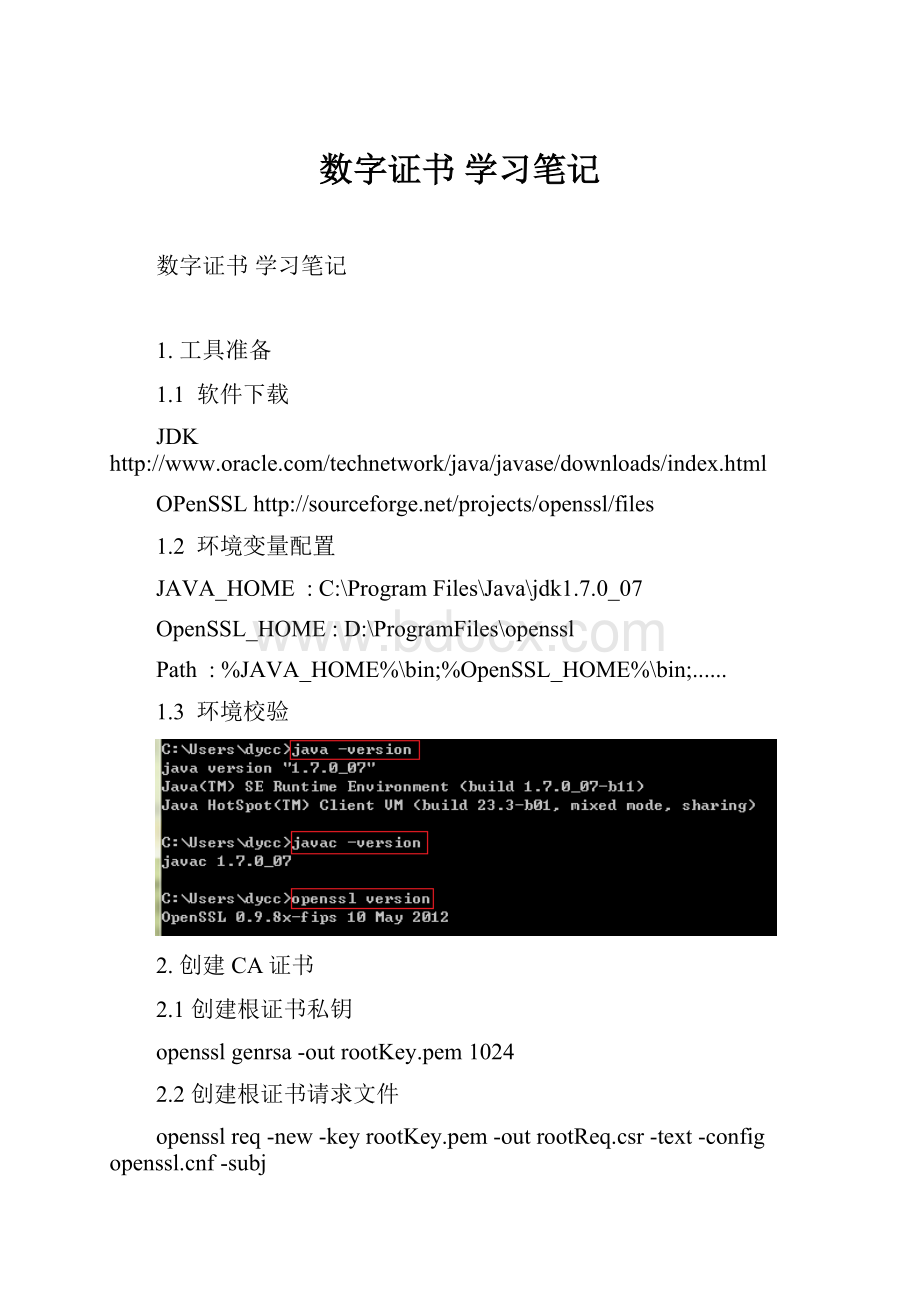
1.3环境校验
2.创建CA证书
2.1创建根证书私钥
opensslgenrsa-outrootKey.pem1024
2.2创建根证书请求文件
opensslreq-new-keyrootKey.pem-outrootReq.csr-text-configf-subj/countryName=CN/stateOrProvinceName=Zhejiang/localityName=Hangzhou/organizationName=MyCompany/organizationalUnitName=MyDept/commonName=localhost/emailAddress=ca@
#注:
f文件可在%OpenSSL_HOME%\bin目录中找到
2.3对根证书请求文件进行自签名
opensslx509-req-inrootReq.csr-outrootCrt.pem-sha1-signkeyrootKey.pem-days3650-text-extfilef-extensionsv3_ca
2.4导出根证书
opensslpkcs12-export-cacerts-inrootCrt.pem-inkeyrootKey.pem-outroot.p12
3.创建Server证书
3.1创建Server证书私钥
opensslgenrsa-outserverKey.pem1024
3.2创建Server证书请求文件
opensslreq-new-keyserverKey.pem-outserverReq.csr-text-configf-subj/countryName=CN/stateOrProvinceName=Zhejiang/localityName=Hangzhou/organizationName=MyCompany/organizationalUnitName=MyDept/commonName=127.0.0.1/emailAddress=server@
3.3使用CA证书对Server证书签名
opensslx509-req-inserverReq.csr-CArootCrt.pem-CAkeyrootKey.pem-CAcreateserial-outserverCrt.pem-days3650-text
3.4导出Server证书
opensslpkcs12-export-clcerts-inserverCrt.pem-inkeyserverKey.pem-outserver.p12
4.创建证书库
4.1创建证书库
keytool-genkeypair-aliastomcat-keyalgRSA-keystoretomcatStore-dname"CN=127.0.0.1,OU=MyDept,O=MyCompany,L=Hangzhou,ST=Zhejiang,C=CN"-keypass123456-storepass123456
4.2创建证书请求文件
keytool-certreq-keyalgRSA-aliastomcat-filetomcatCrtReq.csr-keystoretomcatStore-storepass123456
4.3对证书请求文件进行签名
opensslx509-req-intomcatCrtReq.csr-CArootCrt.pem-CAkeyrootKey.pem-CAcreateserial-outtomcatCrt.pem-days3650
4.4导入CA根证书
keytool-import-aliasroot-keystoretomcatStore-trustcacerts-filerootCrt.pem-storepass123456
4.5导入签名后证书
keytool-import-aliastomcat-keystoretomcatStore-filetomcatCrt.pem-storepass123456
5.Tomcat中配置SSL
5.1单向认证
5.1.1Openssl配置
#修改%TOMCAT_HOME%\server.xml
scheme="https"port="8443"maxThreads="150"
secure="true"SSLEnabled="true"
SSLCertificateFile="../cert/serverCrt.pem"
SSLCertificateKeyFile="../cert/serverKey.pem"
SSLVerifyClient="none"SSLProtocol="all"/>
#将证书复制到%TOMCAT_HOME%\cert目录中
%TOMCAT_HOME%
|_bin
|_cert
||_serverCrt.pem
||_serverKey.pem
|_conf
|_lib
|_webapps
|_...
#启动tomcat访问https,如下图:
https:
//127.0.0.1:
8443/
#导入CA根证书
打开IE->Internet选项->内容->证书->受信任的根证书颁发机构->导入->选择root.p12根证书进行导入->输入导入密码->下一步->完成
#重新访问tomcat,如下图所示IE地址栏中已不再提示证书错误
5.1.2keyStore配置
#修改%TOMCAT_HOME%\server.xml
scheme="https"port="8443"maxThreads="150"
secure="true"SSLEnabled="true"
keystoreFile="cert/tomcatStore"
keystorePass="123456"
clientAuth="false"sslProtocol="TLS"/>
#将证书复制到%TOMCAT_HOME%\cert目录中
%TOMCAT_HOME%
|_bin
|_cert
||_tomcatStore
|_conf
|_lib
|_webapps
|_...
#启动tomcat访问https,如下图:
https:
//127.0.0.1:
8443/
#导入CA根证书
打开IE->Internet选项->内容->证书->受信任的根证书颁发机构->导入->选择root.p12根证书进行导入->输入导入密码->下一步->完成
#重新访问tomcat,如下图所示IE地址栏中已不再提示证书错误
5.2双向认证
5.2.1Openssl配置
#创建Client证书私钥
opensslgenrsa-outclientKey.pem1024
#创建Client证书请求文件
opensslreq-new-keyclientKey.pem-outclientReq.csr-text-configf-subj/countryName=CN/stateOrProvinceName=Zhejiang/localityName=Hangzhou/organizationName=MyCompany/organizationalUnitName=MyDept/commonName=127.0.0.1/emailAddress=client@
#使用CA证书对Client证书签名
opensslx509-req-inclientReq.csr-CArootCrt.pem-CAkeyrootKey.pem-CAcreateserial-outclientCrt.pem-days3650-text
#导出Client证书
opensslpkcs12-export-clcerts-inclientCrt.pem-inkeyclientKey.pem-outclient.p12
#修改%TOMCAT_HOME%\server.xml
scheme="https"port="8443"maxThreads="150"
secure="true"SSLEnabled="true"
SSLCertificateFile="../cert/serverCrt.pem"
SSLCertificateKeyFile="../cert/serverKey.pem"
SSLCACertificateFile="../cert/rootCrt.pem"
SSLVerifyClient="require"SSLProtocol="all"/>
#将证书复制到%TOMCAT_HOME%\cert目录中
%TOMCAT_HOME%
|_bin
|_cert
||_rootCrt.pem
||_serverCrt.pem
||_serverKey.pem
|_conf
|_lib
|_webapps
|_...
#导入CA根证书
打开IE->Internet选项->内容->证书->受信任的根证书颁发机构->导入->选择root.p12根证书进行导入->输入导入密码->下一步->完成
#导入Client证书
打开IE->Internet选项->内容->证书->个人->导入->选择client.p12证书进行导入->输入导入密码->下一步->完成
#启动tomcat访问https,如图:
https:
//127.0.0.1:
8443/
5.2.2keyStore配置
#创建客户端证书库
keytool-genkeypair-aliasclient-keyalgRSA-keystoreclient.p12-storetypePKCS12-dname"CN=127.0.0.1,OU=MyDept,O=MyCompany,L=Hangzhou,ST=Zhejiang,C=CN"-keypass123456-storepass123456
#导出客户端证书
keytool-export-aliasclient-keystoreclient.p12-storetypePKCS12-storepass123456-rfc-fileclient.cer
#将客户端证书导入到服务端证书库中
keytool-import-aliasclient-fileclient.cer-keystoretomcatStore-storepass123456
#修改%TOMCAT_HOME%\server.xml
scheme="https"port="8443"maxThreads="150"
secure="true"SSLEnabled="true"
keystoreFile="cert/tomcatStore"keystorePass="123456"
truststoreFile="cert/tomcatStore"truststorePass="123456"
clientAuth="true"sslProtocol="TLS"/>
#将证书复制到%TOMCAT_HOME%\cert目录中
%TOMCAT_HOME%
|_bin
|_cert
||_tomcatStore
|_conf
|_lib
|_webapps
|_...
#导入CA根证书
打开IE->Internet选项->内容->证书->受信任的根证书颁发机构->导入->选择root.p12根证书进行导入->输入导入密码->下一步->完成
#导入客户端证书
打开IE->Internet选项->内容->证书->个人->导入->选择client.p12根证书进行导入->输入导入密码->下一步->完成
#启动tomcat访问https,如下图:
https:
//127.0.0.1:
8443/
附录
A.常用命令
#用CA证书验证Server证书
opensslverify-CAfilerootCrt.pemserverCrt.pem
#查看证书库的内容
keytool-v-list-keystoretomcatStore-storepass123456
B.创建数字证书的批处理脚本