CCNP实验GRE隧道流量的IPSEC加密.doc
《CCNP实验GRE隧道流量的IPSEC加密.doc》由会员分享,可在线阅读,更多相关《CCNP实验GRE隧道流量的IPSEC加密.doc(5页珍藏版)》请在冰豆网上搜索。
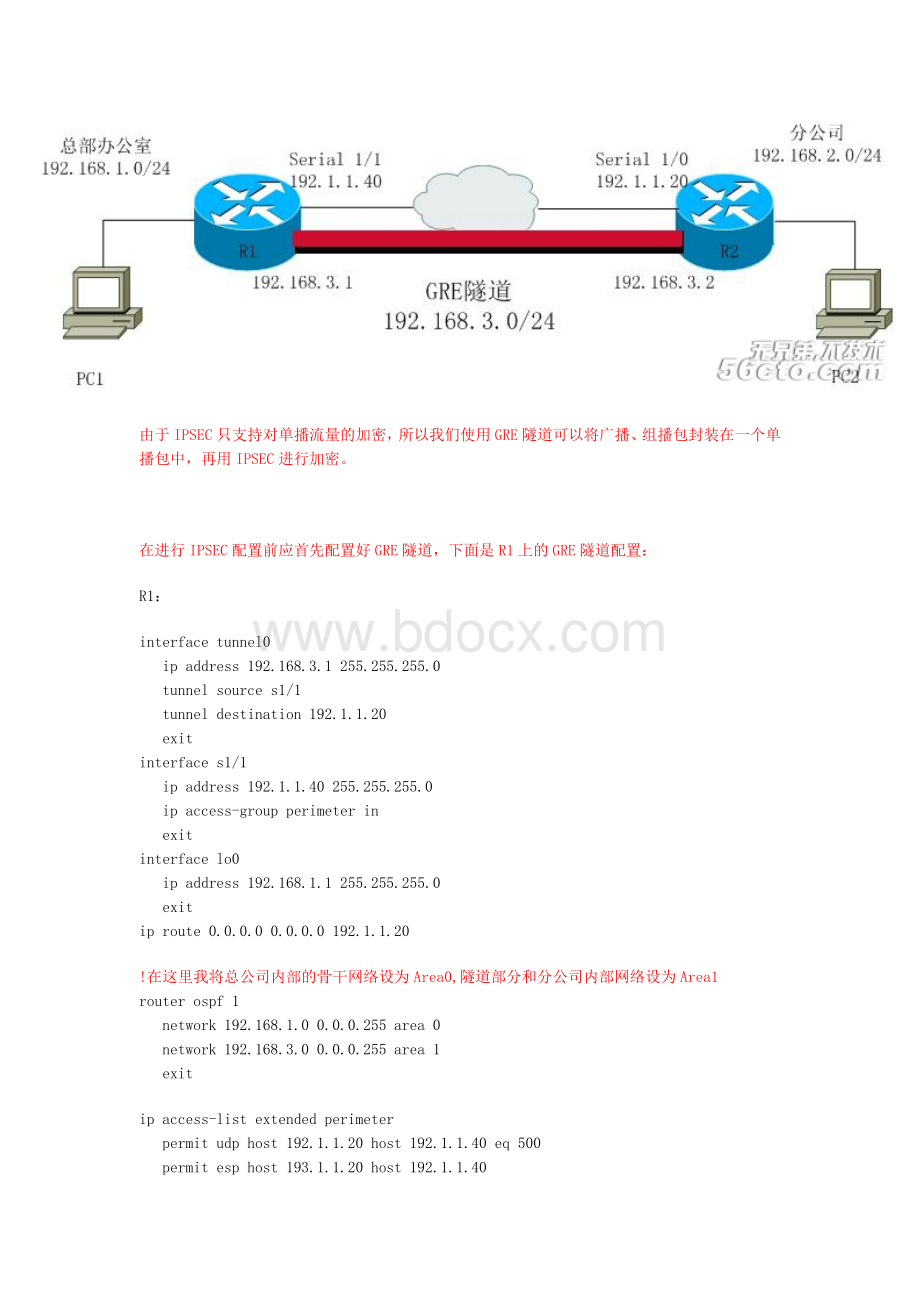
由于IPSEC只支持对单播流量的加密,所以我们使用GRE隧道可以将广播、组播包封装在一个单播包中,再用IPSEC进行加密。
在进行IPSEC配置前应首先配置好GRE隧道,下面是R1上的GRE隧道配置:
R1:
interfacetunnel0
ipaddress192.168.3.1255.255.255.0
tunnelsources1/1
tunneldestination192.1.1.20
exit
interfaces1/1
ipaddress192.1.1.40255.255.255.0
ipaccess-groupperimeterin
exit
interfacelo0
ipaddress192.168.1.1255.255.255.0
exit
iproute0.0.0.00.0.0.0192.1.1.20
!
在这里我将总公司内部的骨干网络设为Area0,隧道部分和分公司内部网络设为Area1
routerospf1
network192.168.1.00.0.0.255area0
network192.168.3.00.0.0.255area1
exit
ipaccess-listextendedperimeter
permitudphost192.1.1.20host192.1.1.40eq500
permitesphost193.1.1.20host192.1.1.40
permitgrehost193.1.1.20host192.1.1.40
denyipanyany
exit
R2:
interfacetunnel0
ipaddress192.168.3.2255.255.255.0
tunnelsources1/0
tunneldestination192.1.1.40
exit
interfaces1/0
ipaddress192.1.1.20255.255.255.0
ipaccess-groupperimeterin
exit
interfacelo0
ipaddress192.168.2.1255.255.255.0
exit
iproute0.0.0.00.0.0.0192.1.1.40
routerospf1
network192.168.2.00.0.0.255area1
network192.168.3.00.0.0.255area1
exit
ipaccess-listextendedperimeter
permitudphost192.1.1.40host192.1.1.20eq500
permitesphost192.1.1.40host192.1.1.20
permitgrehost192.1.1.40host192.1.1.20
denyipanyany
exit
GRE隧道建立好后,就可以进行IPSEC配置了:
R1上的配置:
cryptoisakmpenable
cryptoisakmpidentityaddress
cryptoisakmppolicy10
encryptionaes
authenticationpre-share
group2
hashsha
exit
cryptoisakmpkeycisco123address192.1.1.20no-xauth
!
IPSEC只对进入GRE隧道的流量进行加密
ipaccess-listextendedToR2
permitgrehost192.1.1.40host192.1.1.20
exit
!
这里的GRE隧道是点对点模式的,所以传输集应使用传输模式
cryptoipsectransform-settransesp-aesesp-sha-hmac
modetransport
exit
cryptomapmymap10ipsec-isakmp
matchaddressToR2
settransform-settrans
setpeer192.1.1.20
exit
interfaces1/1
cryptomapmymap
exit
!
最后别忘记删除测试隧道时建立的流量:
ipaccess-listextendedperimeter
nopermitgrehost192.1.1.20host192.1.1.40
R2上的配置:
cryptoisakmpenable
cryptoisakmpidentityaddress
cryptoisakmppolicy10
encryptionaes
authenticationpre-share
group2
hashsha
exit
cryptoisakmpkeycisco123address192.1.1.40no-xauth
ipaccess-listextendedToR1
permitgrehost192.1.1.20host192.1.1.40
exit
cryptoipsectransform-settransesp-aesesp-sha-hmac
modetransport
exit
cryptomapmymap10ipsec-isakmp
matchaddressToR1
settransform-settrans
setpeer192.1.1.40
exit
interfaces1/0
cryptomapmymap
exit
ipaccess-listextendedperimeter
nopermitgrehost192.1.1.40host192.1.1.20
测试实验结果:
r1#shiproute
Codes:
C-connected,S-static,R-RIP,M-mobile,B-BGP
D-EIGRP,EX-EIGRPexternal,O-OSPF,IA-OSPFinterarea
N1-OSPFNSSAexternaltype1,N2-OSPFNSSAexternaltype2
E1-OSPFexternaltype1,E2-OSPFexternaltype2
i-IS-IS,su-IS-ISsummary,L1-IS-ISlevel-1,L2-IS-ISlevel-2
ia-IS-ISinterarea,*-candidatedefault,U-per-userstaticroute
o-ODR,P-periodicdownloadedstaticroute
Gatewayoflastresortis192.1.1.20tonetwork0.0.0.0
C 192.1.1.0/24isdirectlyconnected,Serial1/1
C 192.168.1.0/24isdirectlyconnected,Loopback0
192.168.2.0/32issubnetted,1subnets
O 192.168.2.1[110/11112]via192.168.3.2,00:
00:
17,Tunnel0
C 192.168.3.0/24isdirectlyconnected,Tunnel0
S* 0.0.0.0/0[1/0]via192.1.1.20
R1上pingPC2:
r1#ping192.168.2.1
Typeescapesequencetoabort.
Sending5,100-byteICMPEchosto192.168.2.1,timeoutis2seconds:
!
!
!
!
!
Successrateis100percent(5/5),round-tripmin/avg/max=36/56/84ms
PC1上pingPC2:
r1#ping192.168.2.1sourcelo0
Typeescapesequencetoabort.
Sending5,100-byteICMPEchosto192.168.2.1,timeoutis2seconds:
Packetsentwithasourceaddressof192.168.1.1
!
!
!
!
!
Successrateis100percent(5/5),round-tripmin/avg/max=36/55/104ms