IPseccmd.docx
《IPseccmd.docx》由会员分享,可在线阅读,更多相关《IPseccmd.docx(17页珍藏版)》请在冰豆网上搜索。
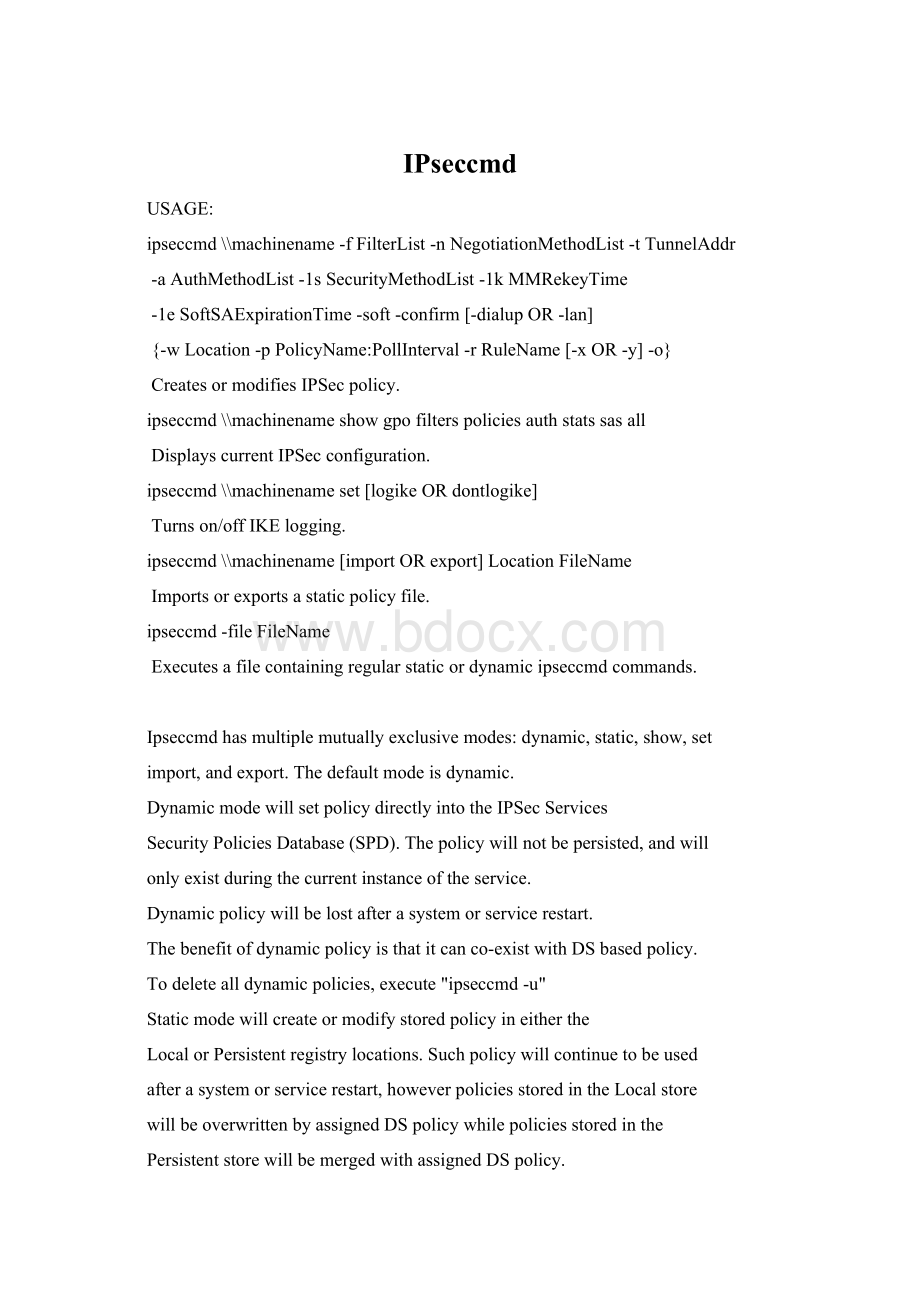
IPseccmd
USAGE:
ipseccmd\\machinename-fFilterList-nNegotiationMethodList-tTunnelAddr
-aAuthMethodList-1sSecurityMethodList-1kMMRekeyTime
-1eSoftSAExpirationTime-soft-confirm[-dialupOR-lan]
{-wLocation-pPolicyName:
PollInterval-rRuleName[-xOR-y]-o}
CreatesormodifiesIPSecpolicy.
ipseccmd\\machinenameshowgpofilterspoliciesauthstatssasall
DisplayscurrentIPSecconfiguration.
ipseccmd\\machinenameset[logikeORdontlogike]
Turnson/offIKElogging.
ipseccmd\\machinename[importORexport]LocationFileName
Importsorexportsastaticpolicyfile.
ipseccmd-fileFileName
Executesafilecontainingregularstaticordynamicipseccmdcommands.
Ipseccmdhasmultiplemutuallyexclusivemodes:
dynamic,static,show,set
import,andexport.Thedefaultmodeisdynamic.
DynamicmodewillsetpolicydirectlyintotheIPSecServices
SecurityPoliciesDatabase(SPD).Thepolicywillnotbepersisted,andwill
onlyexistduringthecurrentinstanceoftheservice.
Dynamicpolicywillbelostafterasystemorservicerestart.
Thebenefitofdynamicpolicyisthatitcanco-existwithDSbasedpolicy.
Todeletealldynamicpolicies,execute"ipseccmd-u"
Staticmodewillcreateormodifystoredpolicyineitherthe
LocalorPersistentregistrylocations.Suchpolicywillcontinuetobeused
afterasystemorservicerestart,howeverpoliciesstoredintheLocalstore
willbeoverwrittenbyassignedDSpolicywhilepoliciesstoredinthe
PersistentstorewillbemergedwithassignedDSpolicy.
ThesyntaxforcreatingpolicyinStaticmodeisalmostidenticaltothatof
Dynamicmode.Thesignificantdifferenceistherequirementofadditional
informationasindicatedbytheoptionslistedinbracesaswellasa
changeinsyntaxforcreatingPermitandBlockfilters.
ShowmodewillquerySPDanddisplayinformationaboutcurrentlyactivepolicy.
SetmodewillchangeIPSecconfigurationparametersforthelifetimeofthe
currentinstanceoftheservice.
Importandexportmodewillimportorexporta.ipsecpolicyfileto/fromthe
localorpersistentstoragelocation.
--------------
DYNAMICMODE
--------------
EachexecutionofipseccmdsetsanIPSecrule,anIKEpolicy,orboth.
OPTIONS:
\\machinenamesetspoliciesonaremotecomputer.Ifnotincluded,
thelocalmachineisassumed.
NOTE:
Ifyouusethisoption,itmustbethefirstargumentAND
youMUSThaveadministrativeprivilegesontheremotecomputer.
ThefollowingparametersareusedtocreateanIPSecpolicy.
Ifomitted,adefaultvalueisusedwhenapplicable.
-fFilterList
Alistofoneormorespaceseparatedfilterspecifications
inthefollowingformat:
A.B.C.D/mask:
port=A.B.C.D/mask:
port:
protocol
Optionally,youcanspecifythekeywordDEFAULTtosetthe
DefaultResponserule
TheSourceaddressisalwaysontheleftofthe'=',
andtheDestinationaddressisalwaysontheright.
Mask:
Optionalsubnetmask.Ifomitted,255.255.255.255willbeused.
Ifsubnetsliealongoctetboundaries,thenyoucanusethefollowing
wildcardnotation:
144.92.*.*isthesameas144.92.0.0/255.255.0.0
128.*.*.*issameas128.0.0.0/255.0.0.0
128.*.*isthesameasabove
128.*isthesameasabove
YoucanreplaceA.B.C.D/maskwiththefollowingforspecialmeaning:
0meansMyaddress(es)
*meansAnyaddress
aDNSname(NOTE:
onlythefirstnameresolutionwillbeset)
DNS,WINS,DHCP,orGATEWAYcanbespecified.SPDwilldynamically
replacesuchsettingswiththeassociatedaddressessetonthecomputer.
PortandProtocolareoptional.Ifomitted,thevaluesaresettoANY
Ifyouindicateaprotocol,aportvalueor':
:
'mustprecedeit.
Youcanusealsousetheseprotocolsymbols:
ICMPTCPUDPRAW
Examples:
M1+M2:
:
6willfilterTCPtrafficbetweenaddressesM1andM2onanyport
172.31.0.0/255.255.0.0:
80+157.0.0.0/255.0.0.0:
80:
TCPwillfilter
allTCPtrafficfromthefirstsubnetandthesecondsubnetonport80.
IFyouwanttofilterProtocol,YoushouldbeUse:
:
followtheDestinationAddr.
MIRRORING:
Ifyoureplacethe'='witha'+',
twofilterswillbecreated,oneineachdirection.
PASSandBLOCKfilters:
Bysurroundingafilterspecificationwith(),
thefilterwillbeaPass(orPermit)filter.Ifyousurroundthe
specificationwith[],itwillbeaBlockfilter.
Example:
(0+128.2.1.1)willcreate2filtersthatwillbeexempted
frompolicy.
NOTE:
ThissyntaxisavailableonlyinDynamicmode.Staticmode
requiressettingoptionsinthenegotiationmethod.
DEFAULT:
Thereisnodefault,-fisrequiredforallDynamiccommands.
-nNegotiationMethodList
Alistofoneormorespaceseparatednegotiationmethodsinthe
followingformat:
ESP[ConfAlg,AuthAlg]RekeyPFS
AH[HashAlg]RekeyPFS
AH[HashAlg]+ESP[ConfAlg,AuthAlg]RekeyPFS
whereConfAlgcanbeNONE,DES,or3DES
andAuthAlgcanbeNONE,MD5,orSHA
andHashAlgisMD5orSHA
NOTE:
ESP[NONE,NONE]isnotasupportedconfiguration.
DEFAULT:
ESP[3DES,SHA]ESP[3DES,MD5]ESP[DES,SHA]ESP[DES,MD5]
Rekey:
OptionalsettingtospecifythenumberofKBytesand/orseconds
afterwhichIKEshouldrekeyaQuickModesecurityassociation.
Addavalueand'k'or's'afterthenegotiationmethodtoindicate
KBytesorseconds.Touseboth,separatethemwithaslash.
Example:
ESP[DES,SHA]5120k/3600swillrekeyafter5MBor1hour
DEFAULT:
100000k/3600s
PFS:
OptionalsettingtoenableQuickModeperfectforwardsecrecy.
Add'PFS'withanoptionalgroupvalueafterthenegotiationmethod:
1,2,or3,correspondingtothefollowingDiffie-Hellmangroups:
DH1-(Low,768bit)
DH2-(Med,1024bit)
DH14-(High,2048bit)
Ifnogroupnumberisspecified,theMainModegroupwillbeused.
Example:
ESP[DES,SHA]P2willsetperfectforwardsecrecytouseDH2
DEFAULT:
PFSisnotenabledbydefault.
-tTunnelAddr
Atunnelmodeendpointinoneofthefollowingformats:
A.B.C.D
DNSname
NOTE:
Ifyouneedtosetupatunnelpolicy,youwillneedtoexecute
ipseccmdtwice--oncefortheoutboundfiltersandoutgoingtunnel
endpoint,andoncefortheinboundfiltersandincomingtunnelendpoint.
DEFAULT:
Omissionoftunneladdressassumestransportmode.
-aAuthMethodList
Alistofspaceseparatedauthenticationmethodsinthefollowingformat:
KERBEROS
CERT:
"",e.g.CERT:
"CN=CA1,OU=O,O=MEME,C=DE,E=ME@here"
PRESHARE:
""
ThestringsprovidedasthepresharedkeyorCAinfoarecasesensitive
andcannotincludequotationmarks.
Youcanabbreviateamethodwithitsfirstletter,i.e.P,K,orC.
DEFAULT:
KERBEROS
-soft
Optionalparametertoallow'soft'securityassociations.
DEFAULT:
Optionisnotset.
-confirm
Optionalparametertoaskforconfirmationbeforesettingpolicy.
NOTE:
OptioncanonlybeusedinDynamicmode.
DEFAULT:
Optionisnotset.
-lan
OptionalparametertosetpolicyonlyonaddressesofLANadapters.
-dialup
Optionalparametertosetpolicyonlyonaddressesofdial-upadapters.
DEFAULT:
Ifneitherparameterisspecified,alllocaladaptersareused.
ThefollowingdealwithMainMode(phase1)policy.
IfnoIKEoptionsarespecified,thecurrentIKEpolicywillbeused.
IfthereisnocurrentIKEpolicy,thedefaultswillbeset.
-1sSecurityMethodList
Alistofoneormorespaceseparatedsecuritymethodsinthe
followingformat:
ConfAlg-HashAlg-GroupNum
whereConfAlgcanbeDESor3DES
andHashAlgcanbeMD5orSHA
andGroupNumcanbe1,2,or3,correspondingtothefollowingDHgroups:
DH1-(Low,768bit)
DH2-(Med,1024bit)
DH14-(High,2048bit)
Example:
DES-SHA-1
DEFAULT:
3DES-SHA-23DES-MD5-2DES-SHA-1DES-MD5-1
-1kMMRekeyTime
ThenumberofQuickModesand/orsecondsafterwhichIKEshouldrekeya
MainModesecurityassociation.Addavaluewith'Q'or'S'toindicate
alimitonQuickModesorseconds.
Touseboth,separatethemwithaslash.
Example:
10Q/3600Swillrekeyafter10quickmodesoreveryhour.
DEFAULT:
NoQuickModelimit,480minlifetime.
-1eSoftSAExpirationTime
Thetimeinsecondstomaintaina'soft'securityassociation.
DEFAULT:
Valueisnotsetif-Softisnotspecified.
ValueissettotheMainModelifetimeif-Softisspecified.
-------------
STATICMODE
-------------
Staticmodeusesmostofthedynamicmodesyntax,butaddsafewoptions
thatenablepolicystorageinthesameformatastheIPSecManagementsnap-in.
WhileDynamicmodeonlyletsyouaddanonymousrulestoSPD,Staticmode
allowsyoutocreatenamedpoliciesandnamedrules.Italsohassome
functionalitytomodifyexistingpoliciesandrules,providedtheywere
originallycreatedwithipseccmd.PoliciescanbesetaseitherAssignedor
Unassigned.OnlyAssignedpolicieswillbeaddedtoSPD.
Inadditiontothenewparameterslistedinbraces,achangeinsyntaxmustbe
madetosignifyfiltersasPass(orpermit)andBlock.InStaticmode,these
optionsaresetintheNegotiationMethodListspecifiedby-n.Therearethree
valuesyoucanpassintheNegotiationMethodListthathavespecialmeaning:
BLOCKwillignoreanymethodsintheNegotiationMethodsListand
willmakeallofthefiltersintheFilterListBlockfilters.
PASSwillignoreanymethodsinNegotiationMethodListand
willmakeallofthefiltersintheFilterListPassfilters.
INPASSwillsetanyinboundfiltersintheFilterListasPassfilterswhile
settingoutboundfilterstousethesecuritymethodsprovided.
Thisisthesameascheckingthe"Allowunsecuredcommunication,
butalwaysrespondusingIPSEC"checkboxinthesnap-in.
StaticModeParameters:
AllparametersareREQUIREDunlessotherwiseindicated.
-wLocation.
Locationtowritepolicych