NAC product.docx
《NAC product.docx》由会员分享,可在线阅读,更多相关《NAC product.docx(21页珍藏版)》请在冰豆网上搜索。
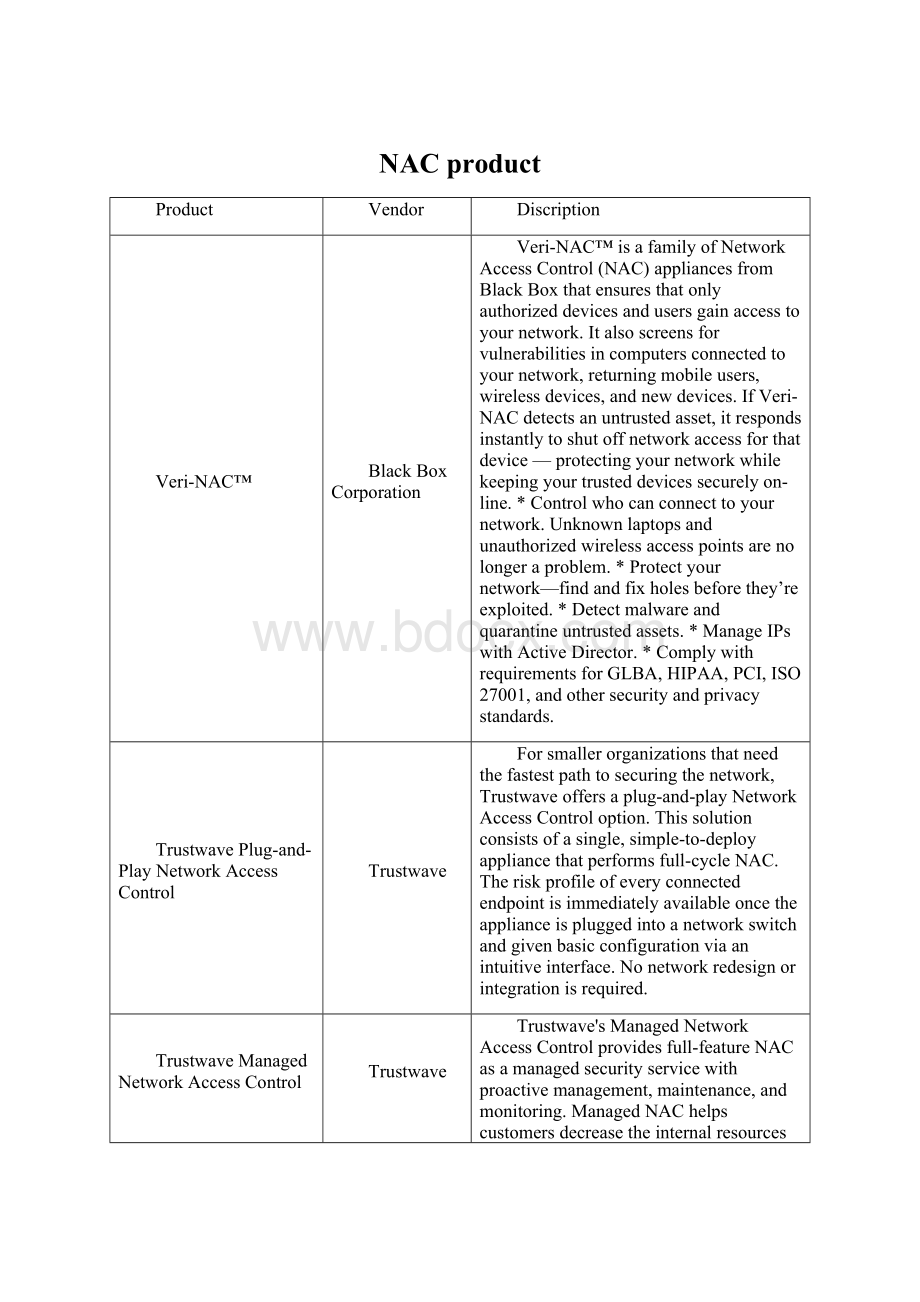
NACproduct
Product
Vendor
Discription
Veri-NAC™
BlackBoxCorporation
Veri-NAC™isafamilyofNetworkAccessControl(NAC)appliancesfromBlackBoxthatensuresthatonlyauthorizeddevicesandusersgainaccesstoyournetwork.Italsoscreensforvulnerabilitiesincomputersconnectedtoyournetwork,returningmobileusers,wirelessdevices,andnewdevices.IfVeri-NACdetectsanuntrustedasset,itrespondsinstantlytoshutoffnetworkaccessforthatdevice—protectingyournetworkwhilekeepingyourtrusteddevicessecurelyon-line.*Controlwhocanconnecttoyournetwork.Unknownlaptopsandunauthorizedwirelessaccesspointsarenolongeraproblem.*Protectyournetwork—findandfixholesbeforethey’reexploited.*Detectmalwareandquarantineuntrustedassets.*ManageIPswithActiveDirector.*ComplywithrequirementsforGLBA,HIPAA,PCI,ISO27001,andothersecurityandprivacystandards.
TrustwavePlug-and-PlayNetworkAccessControl
Trustwave
Forsmallerorganizationsthatneedthefastestpathtosecuringthenetwork,Trustwaveoffersaplug-and-playNetworkAccessControloption.Thissolutionconsistsofasingle,simple-to-deployappliancethatperformsfull-cycleNAC.Theriskprofileofeveryconnectedendpointisimmediatelyavailableoncetheapplianceispluggedintoanetworkswitchandgivenbasicconfigurationviaanintuitiveinterface.Nonetworkredesignorintegrationisrequired.
TrustwaveManagedNetworkAccessControl
Trustwave
Trustwave'sManagedNetworkAccessControlprovidesfull-featureNACasamanagedsecurityservicewithproactivemanagement,maintenance,andmonitoring.ManagedNAChelpscustomersdecreasetheinternalresourcesneededtofullybenefitfromrobustaNetworkAccessControlsolution.
TrustwaveEnterpriseNetworkAccessControl
Trustwave
Trustwave'ssuiteofintegratedappliancesisascalablefull-cycleNetworkAccessControlsolutiondesignedtoprotectlargeenterprisenetworks.Trustwaveoffersfullprotectionforallendpoints,managedandunmanaged,andworksinanynetworkinfrastructure.Oursolutionscombineagent-lessnetworkaccesscontrolwithzero-daythreatpreventionandautomatedpolicyenforcement.Networkintelligenceprovidesaunifiedviewofendpointactivityanddeliverspowerfulanalysisofyournetwork'shistoryandusage.Together,thesefeaturesdelivercomprehensiveendpointcontrol,offeringsecuritychecksthroughoutthelifecycleofadevice'snetworkaccess.TrustwavemanagementserversdelivercentralizedmanagementandmonitoringofNetworkAccessControlappliancesdeployedthroughoutyourenterprise.Alldevicesandpoliciesaremanagedfromacentralmanagementconsoles.
SymantecNetworkAccessControlStarterEdition
SymantecCorporation
SymantecNetworkAccessControlStarterEdition11.0makesitsimpletodeployanetworkaccesscontrolthatcanbeleveragedasyourNACdeploymentsmature.WhenpairedwithSymantecEndpointProtection,itcangrantaccessonlytoendpointsthatcomplywithyourdefinedsecuritypoliciesbyevaluatingcompliancestatus,providingautomaticremediationandensuringaccessisproperlyprovisionedandsecured.
SymantecNetworkAccessControlMobileEdition
SymantecCorporation
SymantecNetworkAccessControlMobileEditionworkswithSymantecEndpointProtectionMobileEditiontoenforcecompliancywithsecuritypoliciesandensuresthatonlysecure,policy-compliantdevicescanaccessthenetworkandemail.SupportsWindowsMobileandSymbiansmartphones,andprovidesover-the-aircentralizedmanagementandreporting.
SymantecNetworkAccessControl
SymantecCorporation
SymantecNetworkAccessControlisanetworksecuritysolutionthatcontrolsaccesstocorporatenetworks,enforcesendpointsecuritypolicyandeasilyintegrateswithexistingnetworkinfrastructures.Regardlessofhowendpointsconnecttothenetwork,Symantec'saward-winningnetworksecuritysolutiondiscoversandevaluatesendpointcompliancestatus,provisionstheappropriatenetworkaccessandprovidesautomatedremediationcapabilities.
SWAT
Wise-MonLtd.
SWATisaSoftwareproductthatgivesoverallsolutionfornetworkaccesscontrol(NAC)basedoncheckingthedevicesthatrequirenetworkservices.SWAThasaneasytousewebbasedmanagementinterfacethatenablespolicydefinitionsandaneventconsolethatprovidesinformationaboutalltheeventsinthenetwork.UsingSWATtheorganizationcancontrolandmonitorthedevicesthatconnectedtotheorganizationnetworkindependentlyofthedevicetypeandinfrastructurevendor.SWATisonethemostreliableNACprogramwithhighefficiencyprovedoverlongperiodoftimesince2004whenitsfirstversionwasreleased.SWATissuccessfullyinstalledingovernmentalagencies,banks,insurance,telecom,healthcare,utilitiesandmore.
StillSecureSafeAccess®
StillSecure
Totalcontroloverthosedangerousendpoints.Whyare5ofthetop7networkswitchvendorspartneringwithusforourSafeAccess®NACtechnology?
Whyhave3branchesoftheU.S.militaryrolledoutmassiveSafeAccessimplementations?
WhyhasSafeAccesswonsomanyofthetopindustryawards?
Becauseitistheworld'sbestsecurenetworkaccesscontrol(NAC)product.SafeAccess:
*Prohibitsguestsfrombringingdownthenetwork*Ensuresdeviceshavethelatestpatchesandhavenotbeencompromised*Isfuture-ready,supportingbothDHCPto802.1xnetworkconfigurations*Stopstheinsiderthreattothenetwork*Givesnetworkadminsreal-timestatusoftheendpointenvironment,lettingthemtakeimmediatedeny/allowactiononindividualdevices*Testsendpointsquicklywithoutinhibitingtheenduser*Rollsoutincontrolled,graduatedphases*Provideshelp-deskuserswithagraphicalheads-updisplayofquarantineddevicesandtheactionsrequiredtoremediatethem*Protectsagainstspywareandmalware.Wedeliveritall:
SafeAccessisacompleteNACsolutionthatstopsunauthorizedaccess,preventsmaliciousendpointactivity,andenforcesyourorganization'ssecuritypolicies.Whenwesayit'sa"complete"solution,wemeanthatSafeAccessdeliversthefullrangeofNACfunctionality:
pre-connecttesting,post-connectmonitoring,enforcementandquarantining,identity-basedmanagement,andremediation.
SophosNetworkAccessControl(NAC)Advanced
Sophos,Inc.
SophosNetworkAccessControl(NAC)Advancedsafeguardsdata.NACAdvancedprotectsinformationbypermittingaccesstotheuserswhoneeditandenablescompaniestocreatecomprehensivesecuritypoliciestocheckthatanycomputeraccessingthenetwork–eventhosenotownedbythecompany-areinfullcompliance.NACAdvancedensuresthatcomputers,includingroaminglaptops,arerunningaspecificanti-virussolutionandhavetheirfirewallsenabled.Compliancewithsecuritypolicies*Benefitfromacomprehensiverangeofover1300pre-definedsecurityapplicationandpatchcomplianceassessments*Isolateanycomputerthatdoesnotmatchyourpolicyuntilitisfixed*Simplifycompliancemonitoringandauditingwithpowerfulreporting,andreal-timeandhistoricaldata
SkyReconStormShield
SkyReconSystems,Inc.
Asorganizationsstruggletofindtherightbalancebetweenbusiness-enablement,businessassetprotection,andregulatory/industry/internalpolicycompliance,thelastthingtheyneedistoaddoverheadtotheiralready-stretchedITresourcesduetoapoorendpointsecuritysolutionimplementation.Organizationsshouldnothavetoaddadditionalheavyagentstotheirendpoints,addmorecomplexitytotheirsecuritymanagementprocesses,norintroduceinefficienciestotheircompliancemanagementandauditingprocesses.Atthesametime,ITorganizationsfindtheyhavelessandlesscontrolovertheirendpoints,whichmayincludetheirservers,desktops,mobilelaptops,andotherdevices.Today'sworkersroutinelyrelyonlaptopswhileathomeandontheroad;theybackupcriticalandsensitiveinformationontoUSBdrivesthatslipinto(andsometimesfalloutof)apocket;oruseanarrayofothernewdevicesfromiPodstodata-capablephonestostoreandshareinformation.Inthisincreasinglymobileandcollaborativeenvironment,business-criticaldataandintellectualpropertyisnowstoredonpersonalcomputersanddeviceswhicharelikelyimproperlymanaged,unmanaged,lacksecurity,orarevulnerabletoemployeemisuse,loss,ortheft.Asaresult,volumesofsensitivedataleavethecorporatefacilityeveryday,leavingitexposedtotheworld.Untilrecently,therehavebeennorealoptionsoutsideofriskavoidancegiventheineffectivenessanddisparityofsolutionsavailableinthemarket.Thedifficultyinproactivelymanagingmobiledevicescoupledwiththesignificantincreaseinincidentsinvolvinglaptoplossanddatatheft,theendpointhaseasilytakenthedubioustitleof"weakestlink"Fortunately,thereareanumberofnewtechnologiesavailabletohelporganizationsovercomethischallenge,givingthemoptionstomitigatetheriskofsystemcompromise,datatheft,dataloss,andsystem/datamisuse.
portnox™
AccessLayers
accesslayers'portnox™isthefirstNACproductthatpracticallychecksforthemostimportantmandatorylegitimateaccessfactor:
Isthedeviceattemptingaccessfromwithinthenetworkisaknownandlegitimatecompanydevice?
isitapprovedtoaccessthenetwork?
AtthispointitshouldbecrystalcleartoanyITprofessionalwhatthey’veknownallalong,that:
ThemainproblemisthedeviceconnectingtotheNetwork,andnotitsantivirusstateorthepatchitlacks.Itisobviousthenthatfirstandforemostweneedtoidentifythedeviceattemptingtoconnectthenetworkbeforeitisgrantedwithaccess.portnox™supportmorethan10differentauthenticationschemescustomizedtoyourneedsandt