密码编码学与网络安全(第五版)答案.docx
《密码编码学与网络安全(第五版)答案.docx》由会员分享,可在线阅读,更多相关《密码编码学与网络安全(第五版)答案.docx(93页珍藏版)》请在冰豆网上搜索。
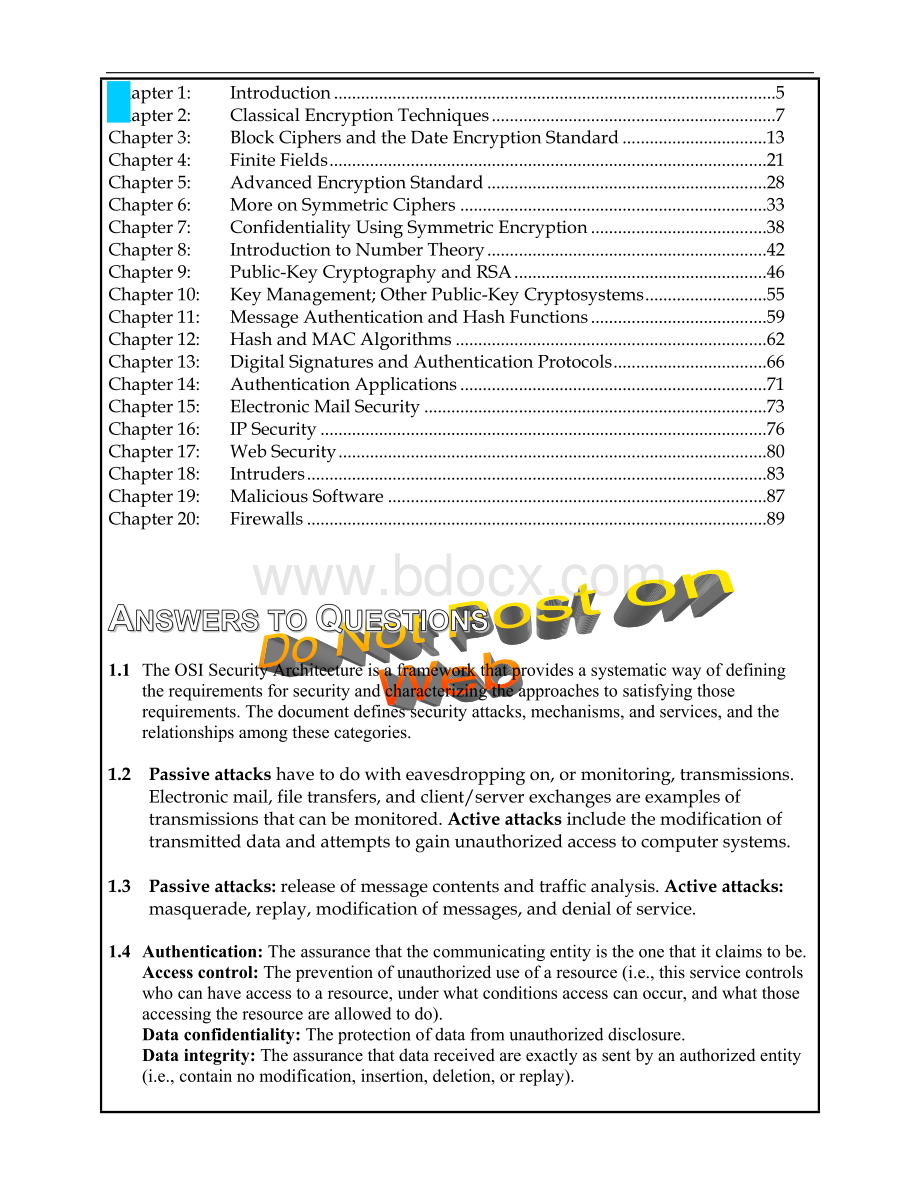
Chapter1:
Introduction 5
Chapter2:
ClassicalEncryptionTechniques 7
Chapter3:
BlockCiphersandtheDateEncryptionStandard 13
Chapter4:
FiniteFields 21
Chapter5:
AdvancedEncryptionStandard 28
Chapter6:
MoreonSymmetricCiphers 33
Chapter7:
ConfidentialityUsingSymmetricEncryption 38
Chapter8:
IntroductiontoNumberTheory 42
Chapter9:
Public-KeyCryptographyandRSA 46
Chapter10:
KeyManagement;OtherPublic-KeyCryptosystems 55
Chapter11:
MessageAuthenticationandHashFunctions 59
Chapter12:
HashandMACAlgorithms 62
Chapter13:
DigitalSignaturesandAuthenticationProtocols 66
Chapter14:
AuthenticationApplications 71
Chapter15:
ElectronicMailSecurity 73
Chapter16:
IPSecurity 76
Chapter17:
WebSecurity 80
Chapter18:
Intruders 83
Chapter19:
MaliciousSoftware 87
Chapter20:
Firewalls 89
AnswerstoQuestions
1.1 TheOSISecurityArchitectureisaframeworkthatprovidesasystematicwayofdefiningtherequirementsforsecurityandcharacterizingtheapproachestosatisfyingthoserequirements.Thedocumentdefinessecurityattacks,mechanisms,andservices,andtherelationshipsamongthesecategories.
1.2 Passiveattackshavetodowitheavesdroppingon,ormonitoring,transmissions.Electronicmail,filetransfers,andclient/serverexchangesareexamplesoftransmissionsthatcanbemonitored.Activeattacksincludethemodificationoftransmitteddataandattemptstogainunauthorizedaccesstocomputersystems.
1.3 Passiveattacks:
releaseofmessagecontentsandtrafficanalysis.Activeattacks:
masquerade,replay,modificationofmessages,anddenialofservice.
1.4 Authentication:
Theassurancethatthecommunicatingentityistheonethatitclaimstobe.
Accesscontrol:
Thepreventionofunauthorizeduseofaresource(i.e.,thisservicecontrolswhocanhaveaccesstoaresource,underwhatconditionsaccesscanoccur,andwhatthoseaccessingtheresourceareallowedtodo).
Dataconfidentiality:
Theprotectionofdatafromunauthorizeddisclosure.
Dataintegrity:
Theassurancethatdatareceivedareexactlyassentbyanauthorizedentity(i.e.,containnomodification,insertion,deletion,orreplay).
Nonrepudiation:
Providesprotectionagainstdenialbyoneoftheentitiesinvolvedinacommunicationofhavingparticipatedinallorpartofthecommunication.
Availabilityservice:
Thepropertyofasystemorasystemresourcebeingaccessibleandusableupondemandbyanauthorizedsystementity,accordingtoperformancespecificationsforthesystem(i.e.,asystemisavailableifitprovidesservicesaccordingtothesystemdesignwheneverusersrequestthem).
1.5 SeeTable1.3.
AnswerstoProblems
1.1
Releaseofmessagecontents
Trafficanalysis
Masquerade
Replay
Modificationofmessages
Denialofservice
Peerentityauthentication
Y
Dataoriginauthentication
Y
Accesscontrol
Y
Confidentiality
Y
Trafficflowconfidentiality
Y
Dataintegrity
Y
Y
Non-repudiation
Y
Availability
Y
1.2
Releaseofmessagecontents
Trafficanalysis
Masquerade
Replay
Modificationofmessages
Denialofservice
Encipherment
Y
Digitalsignature
Y
Y
Y
Accesscontrol
Y
Y
Y
Y
Y
Dataintegrity
Y
Y
Authenticationexchange
Y
Y
Y
Y
Trafficpadding
Y
Routingcontrol
Y
Y
Y
Notarization
Y
Y
Y
Chapter2
ClassicalEncryptionTechniquesr
AnswerstoQuestions
2.1 Plaintext,encryptionalgorithm,secretkey,ciphertext,decryptionalgorithm.
2.2 Permutationandsubstitution.
2.3 Onekeyforsymmetricciphers,twokeysforasymmetricciphers.
2.4 Astreamcipherisonethatencryptsadigitaldatastreamonebitoronebyteatatime.Ablockcipherisoneinwhichablockofplaintextistreatedasawholeandusedtoproduceaciphertextblockofequallength.
2.5 Cryptanalysisandbruteforce.
2.6 Ciphertextonly.Onepossibleattackunderthesecircumstancesisthebrute-forceapproachoftryingallpossiblekeys.Ifthekeyspaceisverylarge,thisbecomesimpractical.Thus,theopponentmustrelyonananalysisoftheciphertextitself,generallyapplyingvariousstatisticalteststoit.Knownplaintext.Theanalystmaybeabletocaptureoneormoreplaintextmessagesaswellastheirencryptions.Withthisknowledge,theanalystmaybeabletodeducethekeyonthebasisofthewayinwhichtheknownplaintextistransformed.Chosenplaintext.Iftheanalystisabletochoosethemessagestoencrypt,theanalystmaydeliberatelypickpatternsthatcanbeexpectedtorevealthestructureofthekey.
2.7 Anencryptionschemeisunconditionallysecureiftheciphertextgeneratedbytheschemedoesnotcontainenoughinformationtodetermineuniquelythecorrespondingplaintext,nomatterhowmuchciphertexti