ASA84 VPN试验系列一IKEv1 L2L.docx
《ASA84 VPN试验系列一IKEv1 L2L.docx》由会员分享,可在线阅读,更多相关《ASA84 VPN试验系列一IKEv1 L2L.docx(8页珍藏版)》请在冰豆网上搜索。
ASA84VPN试验系列一IKEv1L2L
最近一直在研究CCNPSecurityFirewallv1.0,现在基本算是研究完毕了!
发现CiscoASA8.4的变化特别大,真的是越来越像checkpoint防火墙了,不管是NAT还是最近才出现的全局访问控制列表,都和cp防火墙如出一辙。
Firewallv1.0研究完毕后,下一个研究目标就是VPNv1.0,主要介绍ASA上的VPN。
ASA8.4之后的VPN变化也特别大,主要是IKEv2的引入,IOS15.1T(现在好像还下载不了)也开始支持IKEv2了。
可以看出来IKEv2是一个必然的趋势,所以最近我会花不少时间来研究它。
当然研究新技术之前,先了解一下在ASA8.4如何配置传统的IKEv1的VPN是很有必要的。
下面我就对ASA8.4上传统IKEv1L2LVPN进行介绍。
(ASA8.4后续VPN试验会陆续推出)
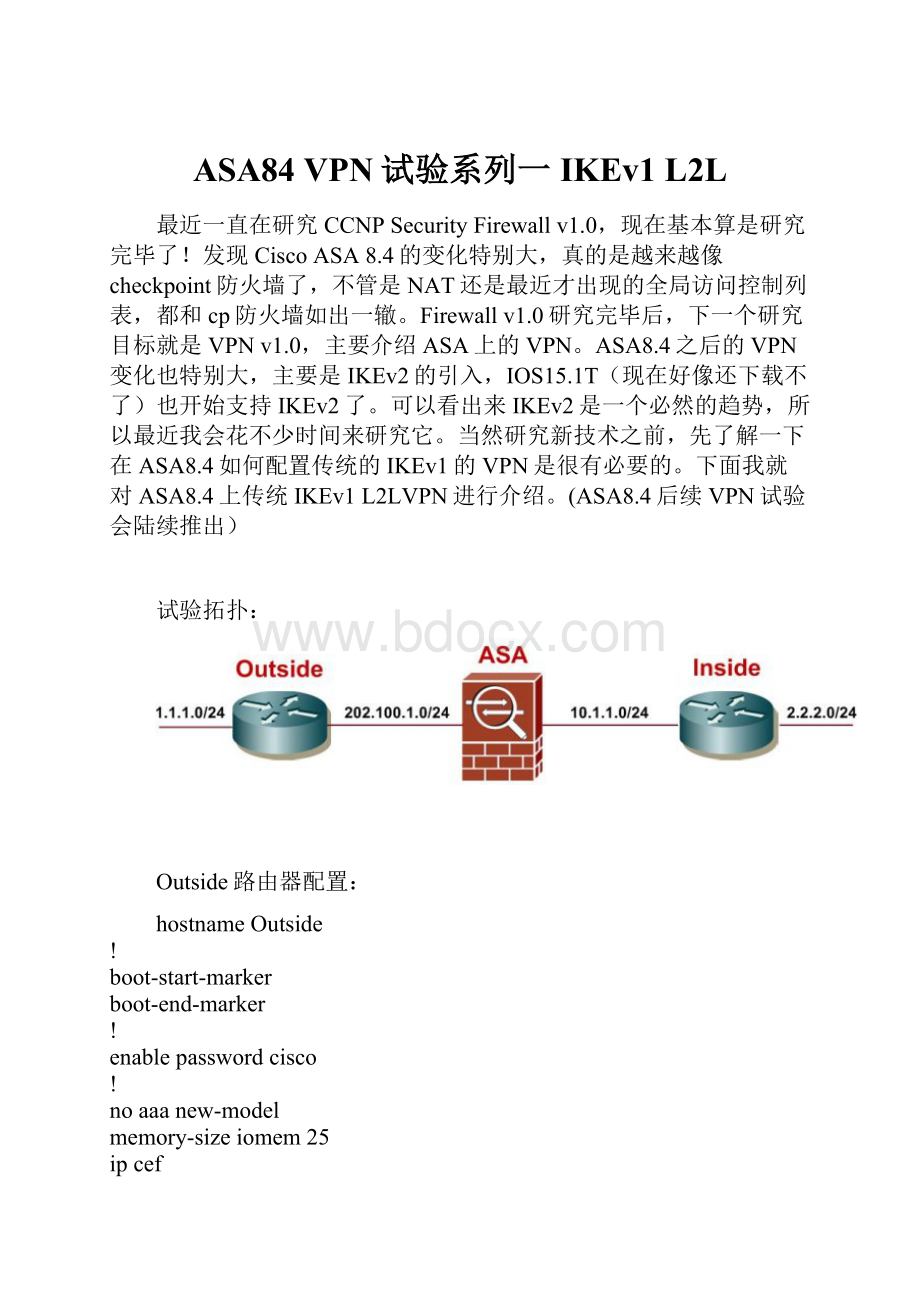
试验拓扑:
Outside路由器配置:
hostnameOutside
!
boot-start-marker
boot-end-marker
!
enablepasswordcisco
!
noaaanew-model
memory-sizeiomem25
ipcef
!
!
!
!
noipdomainlookup
!
multilinkbundle-nameauthenticated
!
!
!
!
!
archive
logconfig
hidekeys
!
!
cryptoisakmppolicy10
authenticationpre-share
cryptoisakmpkeyciscoaddress202.100.1.10
!
!
cryptoipsectransform-setciscoesp-desesp-md5-hmac
!
cryptomapcisco10ipsec-isakmp
setpeer202.100.1.10
settransform-setcisco
matchaddressvpn
!
!
!
!
!
!
interfaceLoopback0
ipaddress1.1.1.1255.255.255.255
!
interfaceFastEthernet0
ipaddress202.100.1.1255.255.255.0
speedauto
cryptomapcisco
!
ipforward-protocolnd
iproute0.0.0.00.0.0.0202.100.1.10
!
!
noiphttpserver
noiphttpsecure-server
!
ipaccess-listextendedvpn
permitiphost1.1.1.1host2.2.2.2
!
!
!
!
control-plane
!
!
linecon0
lineaux0
linevty04
passwordcisco
login
linevty515
passwordcisco
login
!
end
ASA配置:
hostnameASA
enablepassword8Ry2YjIyt7RRXU24encrypted
passwd2KFQnbNIdI.2KYOUencrypted
names
!
interfaceEthernet0/0
nameifOutside
security-level0
ipaddress202.100.1.10255.255.255.0
!
interfaceEthernet0/1
nameifInside
security-level100
ipaddress10.1.1.10255.255.255.0
!
interfaceEthernet0/2
shutdown
nonameif
nosecurity-level
noipaddress
!
interfaceEthernet0/3
shutdown
nonameif
nosecurity-level
noipaddress
!
interfaceManagement0/0
shutdown
nonameif
nosecurity-level
noipaddress
management-only
!
ftpmodepassive
objectnetworkInside-Router-Loop0
subnet2.2.2.0255.255.255.0
objectnetworkRemote-vpn-address
subnet1.1.1.0255.255.255.0
access-listvpnextendedpermitiphost2.2.2.2host1.1.1.1(感兴趣流)
pagerlines24
mtuOutside1500
mtuInside1500
nofailover
icmpunreachablerate-limit1burst-size1
noasdmhistoryenable
arptimeout14400
nat(Inside,Outside)sourcestaticInside-Router-Loop0Inside-Router-Loop0destinationstaticRemote-vpn-addressRemote-vpn-address(使用TwiceidentityNAT旁路掉VPN感兴趣流)
!
objectnetworkInside-Router-Loop0(普通上网用PAT)
nat(Inside,Outside)dynamicinterface
routeOutside0.0.0.00.0.0.0202.100.1.11(解决路由问题)
routeInside2.2.2.2255.255.255.25510.1.1.11
timeoutxlate3:
00:
00
timeoutconn1:
00:
00half-closed0:
10:
00udp0:
02:
00icmp0:
00:
02
timeoutsunrpc0:
10:
00h3230:
05:
00h2251:
00:
00mgcp0:
05:
00mgcp-pat0:
05:
00
timeoutsip0:
30:
00sip_media0:
02:
00sip-invite0:
03:
00sip-disconnect0:
02:
00
timeoutsip-provisional-media0:
02:
00uauth0:
05:
00absolute
timeouttcp-proxy-reassembly0:
01:
00
dynamic-access-policy-recordDfltAccessPolicy
nosnmp-serverlocation
nosnmp-servercontact
cryptoipsecikev1transform-setciscoesp-desesp-md5-hmac(第二阶段转换集)
cryptomapcry-map10matchaddressvpn(cryptomap配置)
cryptomapcry-map10setpeer202.100.1.1
cryptomapcry-map10setikev1transform-setcisco
cryptomapcry-mapinterfaceOutside(调用cryptomap到外部接口)
cryptoikev1enableOutside(外部接口激活IKEv1)
cryptoikev1policy1(IKEv1第一阶段策略)
authenticationpre-share
encryptiondes
hashsha
group1
lifetime86400
telnettimeout5
sshtimeout5
consoletimeout0
threat-detectionbasic-threat
threat-detectionstatisticsaccess-list
nothreat-detectionstatisticstcp-intercept
webvpn
anyconnect-essentials
tunnel-group202.100.1.1typeipsec-l2l(tunnel-group配置)
tunnel-group202.100.1.1ipsec-attributes
ikev1pre-shared-keycisco
!
class-mapinspection_default
matchdefault-inspection-traffic
!
!
policy-maptypeinspectdnspreset_dns_map
parameters
message-lengthmaximumclientauto
message-lengthmaximum512
policy-mapglobal_policy
classinspection_default
inspectdnspreset_dns_map
inspectftp
inspecth323h225
inspecth323ras
inspectrsh
inspectrtsp
inspectesmtp
inspectsqlnet
inspectskinny
inspectsunrpc
inspectxdmcp
inspectsip
inspectnetbios
inspecttftp
inspectip-options
!
service-policyglobal_policyglobal
prompthostnamecontext
Cryptochecksum:
1b511154bb6ceb038c38677ae2b15c67
:
end
Inside路由器配置:
hostnameInside
!
boot-start-marker
boot-end-marker
!
!
noaaanew-model
ipcef
!
!
!
!
!
multilinkbundle-nameauthenticated
!
!
!
!
!
archive
logconfig
hidekeys
!
!
!
!
!
!
!
interfaceLoopback0
ipaddress2.2.2.2255.255.255.255
!
interfaceFastEthernet0
ipaddress10.1.1.1255.255.255.0
speedauto
!
ipforward-protocolnd
iproute0.0.0.00.0.0.010.1.1.10
!
!
noiphttpserver
noiphttpsecure-server
!
!
!
!
control-plane
!
!
linecon0
lineaux0
linevty04
!
end